Is Your Security Awareness Program a Total Snoozefest?
So you put everyone in a room (or video call) and run through your security policy. You checked the compliance boxes for HIPAA, SOC 2, GDPR, PCI-DSS, or NIST data privacy regulations. You’re all set, right?
Not so fast.
Most run-of-the-mill check-box-style security awareness programs leave companies vulnerable to cybercrimes, such as phishing attacks, data breaches, social media scams, malware and ransomware, social engineering attacks, physical security breaches, etc.
And it’s not due to a lack of employee engagement either. In our recent Shadow IT study, we found that 74% of employees believe security training is effective. That’s great news!
The not-so-great news is that we also found that of the companies we surveyed, 41% of them only provide security training once a year.
A poorly-designed and infrequent cybersecurity awareness program isn’t just ineffective. It can even create a false sense of security and cause employees to let their guard down — exposing your company’s sensitive information to an increased risk of security breaches!
Is your security awareness training doing what it’s supposed to do?
Read on to see why your cybersecurity awareness training program might be failing and what you can do to improve it.
Are You Making These Mistakes in Your Security Awareness Training Program?
The first step in solving the problem is understanding what the problem is. You may be making a few mistakes that set your security awareness training program up for failure. Let’s talk through some of the most common but often overlooked blunders companies make.
Shaky foundation
A significant reason cybersecurity training programs fail to be effective is that they start off on the wrong foot. The foundations laid are shaky, with end-users totally disengaged from security. But don’t be quick to blame it on the users; there’s a reason for that lack of interest.
Here at Kolide, we believe that end-users can make rational and informed decisions about security risks when educated and honestly motivated. We’ll come back to the education part; first, let’s focus on “honestly motivated.”
If you want to motivate people to do something, you need to show them why it’s worth their while. Most end-users don’t inherently understand the importance of cybersecurity (often because security training has failed to show them how it is relative to their day-to-day activities).
This motivation is also affected by the relationship between the security team and end-users. Are they known for being helpful, open to communication, and honest? Or perhaps they’re seen as the stonewaller and challenging to work with? If the security team doesn’t act as though they care about the rest of the company’s needs, it shouldn’t come as a surprise when end-users return the favor. For this reason, it’s important to communicate how security relates to every part of the organization.
No plan in sight
Remember what we said earlier; end-users need to make informed security decisions? We talked about honest motivation; now, let’s look at the education required for end-users to succeed in security.
It’s not as easy as many companies make it out to be. Cybersecurity training programs are often ad-hoc and lack a long-term plan. Without a solid framework that includes milestones, actionable goals, and further integration into your company’s culture, employees often fail to develop a sense of responsibility. Not to mention, they’re left wondering about their roles in the company’s cybersecurity policy.
One and done mentality
Ad-hoc training makes another critical mistake: thinking that one, Powerpoint-led training session a year will suffice.
Sure, you’ve probably met your compliance goals, but your company’s overall security is suffering when security awareness training isn’t carefully considered and planned out. Only offering annual training means you’ve got a lot to cover in that one session. It usually turns into an information dump where the audience is given more than they can digest and act on. With information overload, end-users will likely only retain a tiny portion of the content. Rome wasn’t built in a day, and neither are cybersecurity rockstars.
Moreover, a typical Powerpoint presentation often lacks the interactivity to help the audience retain information and understand how they can apply the training to their day-to-day activities.
Over-generalization and failure to engage
No matter how comprehensive your security awareness training modules are, you won’t get employees to pay attention (much less retain the information) if a presentation is boring and the security topic is irrelevant. If you pile on facts and statistics without making them relatable, you will fail to make the content stick.
It’s common to lump the entire company into one session and generalize training across the board. For some topics, that may work. But you also risk being overly technical or talking down to specific groups of end-users. It’s nearly impossible to offer security content that is relevant and appropriate for the audience when you have marketing, support, development, and more all in attendance. The security awareness training program will fail to engage end-users if the content isn’t relevant to their responsibilities or doesn’t match their technical competence.
Looking for trouble
Many companies send phishing emails to employees as part of their cybersecurity training program. These simulations sometimes feel like security teams are looking for trouble. If conducted with a “gotcha” approach that pits end-users against IT, it diminishes their cooperation. There’s no system of praise and rewards, but instead, one that looks for opportunities to punish. This can significantly affect the relationship between employees and security teams by breeding fear, secrecy, and disengaged end-users.
How To Build a Security Awareness Program That Works
This may feel a bit overwhelming, but don’t give up just yet. Your cybersecurity awareness training has hope, and you only need to follow a few steps to get it back on track.
1. Expand your security awareness training program
We all know that the “one and done” approach to training doesn’t work, yet many organizations still do it because expanding the security training program is too daunting or time-consuming. It doesn’t have to be, though; expanding training doesn’t necessarily mean drastically increasing the workload for the security or IT team. And the effort put towards training will always pay off in the long run.
Without a plan that goes further than an annual session, training will likely be viewed as either an obligation for some compliance request or a punishment to be endured when something goes wrong. This means your audience enters training with a negative mindset; there’s nothing fun or interesting about security training, and you’re already losing the battle.
One easy way to integrate security training more regularly is by sending out emails that act as newsletters or explain current cybersecurity happenings (like the cause of recent data breaches or the importance of a new software patch). Creating trivia or puzzles from security policies is another fun way to test the company’s knowledge. And when you’ve got the time and resources to make it happen, offering training on specific topics or geared towards certain departments are great investments into your security training program.
However you go about it, building out your training program shows genuine interest in employee development. The security team is devoted to helping end-users understand and excel in security.
If you’re still using the excuse that you don’t have time to expand your security training program, consider this: if you don’t have the time to develop training now, when will you have time to fix the cybersecurity mistakes made by uninformed end-users?
2. Adjust your tone
A lot can be accomplished by reevaluating the tone and voice you use in training. Security training has a history of heavily utilizing fear-based tactics, which will only invoke fear and anxiety. Instead, shift towards a positive approach to security and be sure your tone reflects that. If you can successfully do so and begin to educate with empathy , you’ll have won half the battle.
To do this, first, consider what technical terms you may use in training that can either confuse the audience or be misinterpreted. Let’s be honest; some security jargon comes off pretty scary. Take “zero trust,” for instance. To someone who isn’t familiar with the idea and isn’t deep into the security realm, this can sound like the security team saying, “we don’t trust you,” which (hopefully) isn’t the case. If not scary, some terms can be confusing if you’ve never heard them before. Instead, talk in terms that your audience is familiar with and when something might sound unintentionally scary, take the time to explain it further.
Using specific scenarios or statistics to scare end-users into compliance is often a no-go. Consider making up a silly story instead of conjuring up fear with doomsday scenarios when you need an example to drive the point home. We’re willing to bet that end-users prefer to leave training laughing over shuddering.
Security can already feel elusive and scary to the average person, so do your best not to add to that negative connotation. Position your content as recommendations to inform, educate, and empower employees. Using a positive tone and catering your voice to fit the audience will create confident security advocates from end-users and support long-term investments into security.
3. Encourage persona experiences that create investments in cybersecurity
Most employees want to do their best at work, and they’ll follow recommendations if you use relevant messaging and share meaningful and actionable advice in real-time to help them do their job better.
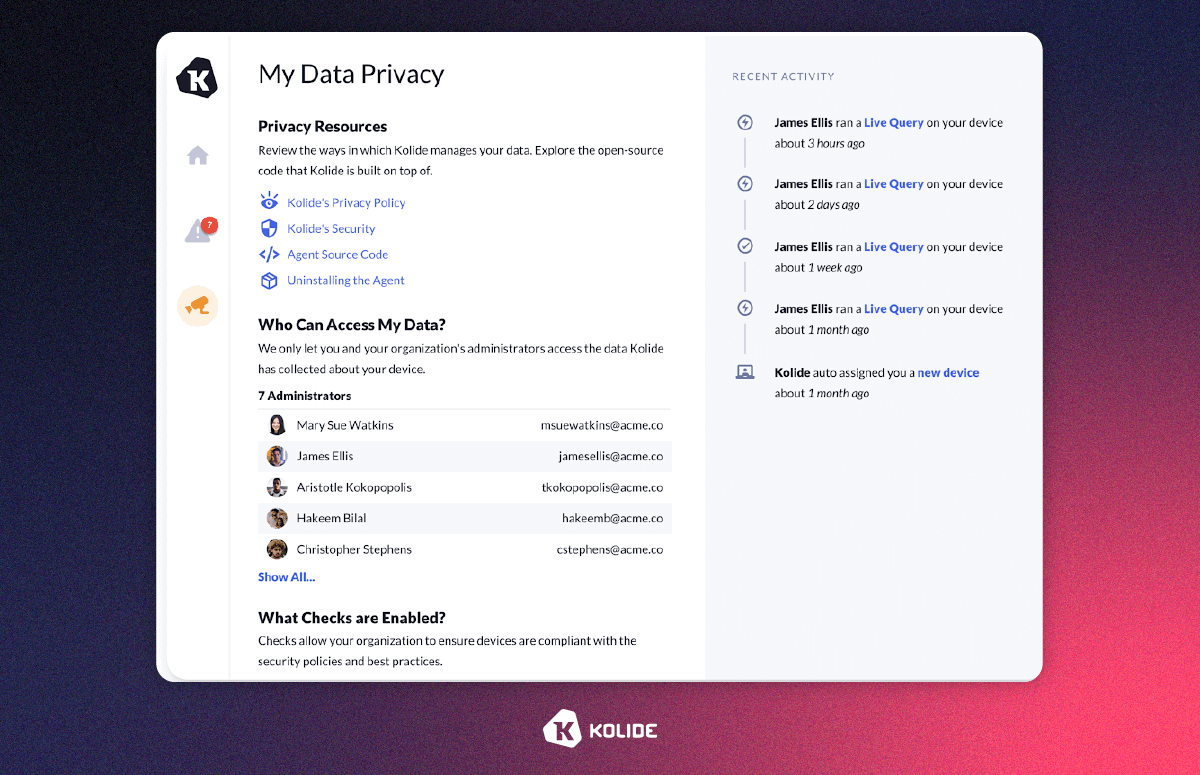
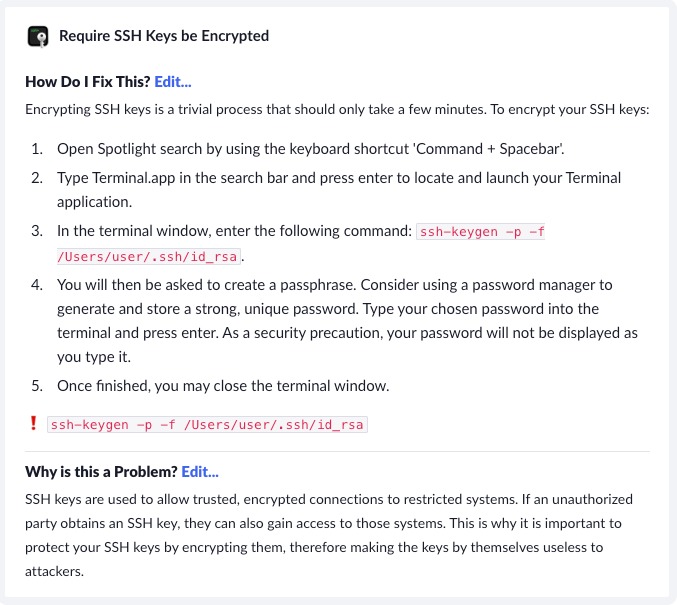
For example, Kolide notifies users when a security issue is detected. You can craft the recommendation to explain why the end-user receives the message and offer actionable instructions to remove the security risk. The content is relevant to the employee when it’s delivered, and they can learn through action to build good cybersecurity habits.
Another way to personalize the experience end-users have with cybersecurity is to integrate appreciation and praise into your training program. When people feel good about their decisions, it turns into empowerment, and they’re more likely to become invested members of your cybersecurity defenses.
4. Support employees outside of training sessions
An essential part of your security awareness training program is understanding that it’s not just about the training. Instead of creating a company culture that thinks about security only when they are actively being talked to about it, you should aim to make security the default at all times.
A good training program is about strengthening your front lines: people. To effectively meet this goal, you need to also set end-users up for success by making security the default. What does that mean? Generally, it consists of making sure the path to security-minded decisions is either the only option or the path of least resistance.
People make mistakes, and that’s both inevitable and understandable. We should not expect them to be perfect, no matter how much training they’ve had. It’s important to recognize that and make security easy to participate in. An example of this is following the principle of least privilege. If you’re only giving employees access to the data they need to do their job, you’re no longer relying on them to protect all of your company’s data. It’s easier on everyone and, therefore, more likely to succeed. This also allows you in training to focus on why policies are in place instead of how you follow them, which creates more mindful and informed end-users.
Your Security Awareness Program Doesn’t Have To Be a Snoozefest
It’s time to ditch the PowerPoint presentations riddled with hard-to-understand security policies and make your cybersecurity education digestible, relevant, and actionable. Fine tuning your goals and changing the mindset that surrounds security training can make a world of difference, and before you know it you’ll have a strong frontline of highly invested cybersecurity advocates.
You don’t have to reinvent the wheel to achieve the ideal security awareness program.
Kolide augments your security awareness program by guiding employees to turn what they learn into action. They can develop good user behaviors and a culture of security through hands-on, in-situation, and practical experiences by following recommendations delivered via our Device Trust solution at the point of cloud app login.
Employees can understand how your security policy applies to their job functions and follow recommendations to reduce risks without compromising productivity. The open channel can also help you gather more feedback from end-users. The insights can help shape your security strategy while increasing employee buy-in and participation.
Watch our on-demand demo and see how you can crowdsource information security and make every end-user part of the solution.























