New Checks: Plain-Text MFA Codes Now Available on Windows and Linux
We are excited to announce the immediate availability of six new checks that complete our check coverage of looking for plain-text multi-factor codes and recovery documents for GSuite, Github, and 1Password.
These recovery documents are essentially plain-text passwords that allow anyone who has them to bypass the multi-factor prompt on their respective services.*
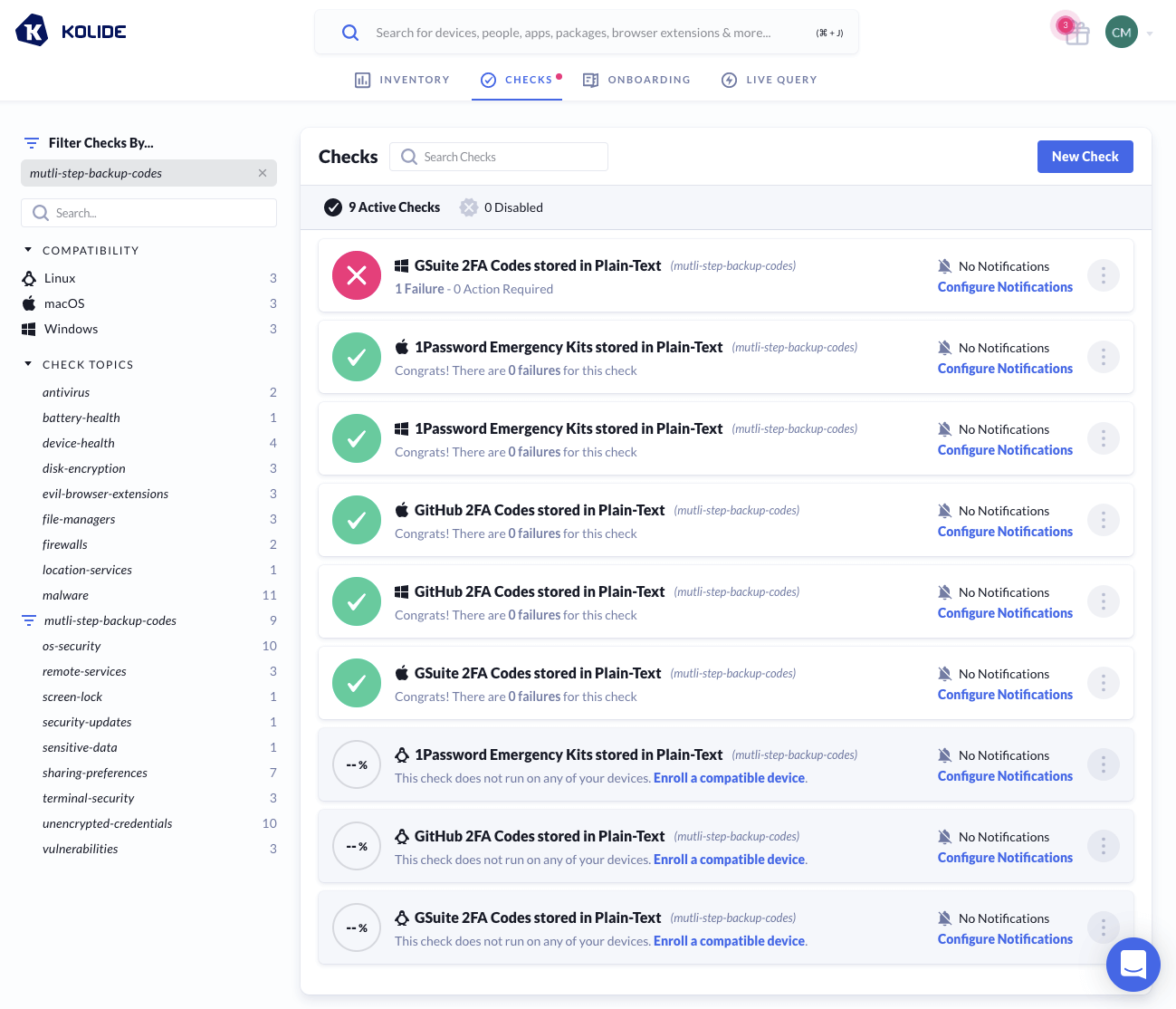 Like all new checks we ship, they are enabled by default, but will not produce any notifications for you or your users until a team-member configures them to do so. You can review these new checks by clicking on the “multi-step-backup-codes” topic on the Checks page.
Like all new checks we ship, they are enabled by default, but will not produce any notifications for you or your users until a team-member configures them to do so. You can review these new checks by clicking on the “multi-step-backup-codes” topic on the Checks page.
If you have any questions or feedback on these checks, or would like to see similar checks for additional services, please let us know.
* An exception to this statement should be noted for 1Password’s Emergency Kits. While these kits do contain sensitive data like the vault’s secret key and sign-in address, it requires the user to explicitly write down their master password for it to grant a bad actor full access to their vault.