Our Startup's SOC 2 Compliance Journey
Hello and welcome to the only guide to SOC 2 compliance for people who never expected themselves to be reading an article on this subject.
If you’re reading this, you’re likely in the same position I was when I started my SOC 2 compliance journey. You know SOC 2 certification is a helpful piece of third party proof that your company handles data responsibly. You’re hopeful it can help you close deals, secure funding, and generally prove that your organization is actually organized. And like me, you’re probably intimidated or just confused by the audit process.
The good news is, you can relax–there are no stupid questions here. I should know, because I have asked them all.
As someone who has been through the process, I’d like to share my experience in getting my SaaS startup SOC 2 compliant. And along the way, I hope I can answer some questions and bust some myths.
Why I Wanted SOC 2 Certification
When I joined Kolide in 2017, I was the first operations hire at an eight-person startup. I soon received my first security questionnaire from a prospective customer. It had over 100 questions, was full of acronyms I couldn’t decipher, and asked for plans, policies, and procedures that I had never heard of.
Pre-SOC certification, the only solution was to spend hours filling out each questionnaire, usually with the collaboration of, our CEO. It wasn’t the best use of his time or mine, but we had to complete the vendor management process in order to sign on new customers.
Slowly but surely, we reviewed and polished off existing documents, wrote new ones, and set a schedule to review them on at least an annual basis. Here is a list of documents we either wrote or edited, in no particular order:
- Software Development Life-Cycle
- Information Security Policy
- List of Sub-Processors
- Risk Assessment Process
- Product Architecture Diagram
- Incident Response Plan
- Data Classification Policy and Handling
- Business Continuity and Disaster Recovery Plan
- SaaS Architecture Security
- Vendor Management Policy
- Onboarding/Employee Life Cycle and Access Levels
And then I noticed something: most of these questionnaires started by asking if we had a compliance audit report, usually SOC 2. I wondered–if we got a SOC 2 compliance report, would that reduce the number of questionnaires we had to complete? Would it demonstrate to our customers all of the security measures we take to mitigate potential risk to ourselves and them? What even IS SOC 2 compliance, and how does one achieve it?
Off to Google I went. I learned the basics: that SOC 2 is a voluntary framework established by the American Institute of CPAs (AICPA) to assess how organizations manage customer data. I found out that certification is generally considered to be table stakes for any SaaS company above a certain risk threshold. I searched for the benefits of SOC 2, the difference between SOC 2 Type I vs SOC 2 Type II, how much it costs, and I got to read fun articles like the 5 Ways You Could Derail Your SOC 2 Audit.
The benefits certainly seemed aligned with our needs. Undergoing a SOC 2 audit would help us tighten up our own security posture, and demonstrate to our customers that we took security and compliance as seriously as they do. Further, we would be able to present this document for annual vendor reviews, and likely some initial security reviews, rather than going through the extensive questionnaires we were receiving.
And there was another reason I was interested in getting SOC 2 certified: I was hearing a lot about it from our customers. Specifically, I found out that many of them were using Kolide (which is an endpoint security product) to prove their own compliance. We helped them with inventory management, so they could show things like whether or not they had SSH keys encrypted or firewalls enabled. I wanted to understand something that was clearly a value proposition for us, so we could be more empathetic to our customers’ compliance needs.
The SOC 2 Certification Process
Deciding to get SOC 2 certified was one thing, but making it happen was something else entirely. And while I want to say upfront that the process wasn’t as complicated as I’d originally feared, it was still a lot of work. (And a lot of spreadsheets.)
Step 1: Buy-in
The first step to becoming SOC 2 compliant was persuading our CEO that it was a worthwhile project. After all, the process can cost anywhere from $10k to $150k, which was a big upfront investment for us. But I was able to prove we’d more than make it back from time saved and deals closed.
The tougher matter was figuring out how to comply with SOC 2 requirements that conflicted with our existing processes. For example, there was a code review requirement that would have slowed us way down, especially as a young startup. But our auditors were willing to be flexible about this point, and after several meetings about it, we came up with a compromise that made everybody happy.
Step 2: Finding SOC 2 auditors
SOC 2 audits can only be performed by an auditor at a licensed CPA firm, preferably one with cybersecurity experience. I opted to work with a local CPA firm (at the time, I was living in Boston, MA) and found Wolf & Company. I met with them to learn more about the process, and the differences between Type I and Type II.
Since we were small, and I was new at this, SOC 2 Type I seemed to be the best approach, as it only reviewed our internal documentation, policies, and procedures from one point in time, versus a SOC 2 Type II which looked at these items over the course of 6 months to a year.
Wolf sent us a proposal for the project, including the cost, and recommended a local consultant that could help us with the process. From there, we scheduled a Readiness Review, which was basically a pre-SOC 2 review to help us determine any gaps that would prevent us from being compliant. Before I got the review, I was bullish on doing the majority of the work myself; how hard could it really be? Famous last words.
The Readiness Review turned out to be 38 pages of feedback on every aspect of our business, and recommendations on how to fix every “gap.” The recommendations ranged from low-hanging fruit (make an org chart) to tougher requests (have a vendor assessment reviewed and approved by a designated committee on an annual basis).
For most issues, the problem wasn’t that we weren’t compliant, it was that I didn’t know how to prove that we were. For instance, they asked us to prove we had multifactor authentication enabled in Heroku. But how? Well, it turns out a screenshot would suffice. And a lot of our compliance involved simple things like screenshots or even live demonstrations of our processes.
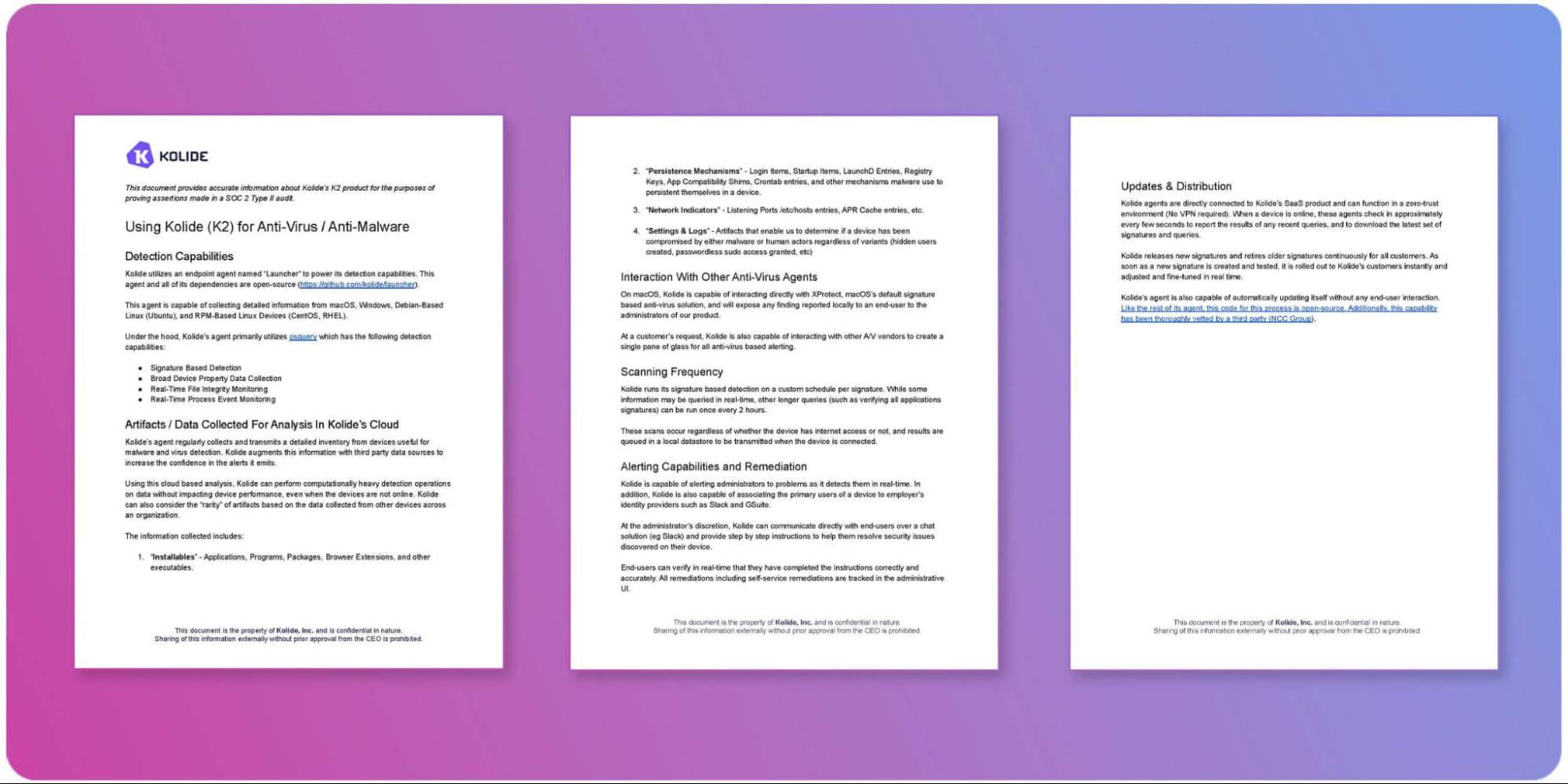
I quickly gained a new understanding of why our customers rely on Kolide to prove compliance, since I leaned on our product to prove a host of things about our company devices, including that they had:
- Disk encryption
- Firewalls enabled
- Password managers installed
- Operating systems up-to-date
- Screen lock enabled
Even so, I soon got overwhelmed by the sheer amount of evidence I had to gather. I finally admitted I needed some help, and the auditors at Wolf suggested New England Safety Partners to help us get audit-ready.
I chose NESP over the automated compliance support products out there, because they were local and it was important to me (pre-COVID) to be able to have face-to-face interactions, and feel like I was working with people who had a personal stake in our company. I met with them every week for 3 months, and they worked with me to gather the evidence I needed.
Check out Do Macs Need Third-Party Antivirus for SOC 2 Compliance?
Or Is Windows Defender Enough to Pass SOC 2?
Step 3: The SOC 2 audit
Then came the audit itself, which entailed daily meetings for 2 weeks of meetings with Wolf, in which we went over all the documentation I’d gathered, and walked them through our processes. This is when I was most grateful for New England Safety Partners, for advocating for me anytime there was an issue I didn’t understand or that I wanted to push back on.
At the end of the process, we walked away with a 31-page report documenting everything from our weekly all-hands schedule to our spam blocker. We had our SOC 2 Type I certification, and I would never have to go through the process again.
Just kidding!
A year later we got SOC 2 Type II. And while the second go-round was certainly easier, since I wasn’t starting from scratch, it was also more expensive and complex. So, if you do choose to pursue SOC 2 certification, keep in mind that the annual process isn’t so much a “renewal” as a whole new review.
Maintaining SOC 2 compliance year after year poses particular challenges for rapidly growing startups. Since our original audit, we’ve more than doubled in size, and some of the evidence I gathered manually the first time around has now expanded to the point that I’m investigating automated solutions for things like vendor management.
So the moral of the story is that, like most things in life, SOC 2 compliance is never really finished; it’s a continual process of examining and refining how you do business.
SOC 2 FAQs
Was the SOC 2 audit worth it?
In our case, yes! We got what we wanted out of our audit: shorter turnaround time for security questionnaires and annual vendor security reviews, as well as increased understanding and empathy for our customers and their needs.
Did SOC 2 force your company to make significant changes?
Not really. As a security company, we’d already developed rigorous processes for managing data and planning for contingencies. Even so, that level of external accountability has given us a concrete reason to continually tighten our security posture.
I compare it to housekeeping; I keep a clean house even when there’s no one else around, but if company is coming over, I’ll be scrubbing the baseboards with a toothbrush.
Does SOC 2 certification mean a company is completely secure?
Emphatically no. SOC 2 isn’t a pass/fail test where you’re trying to prove you have zero vulnerabilities. If it were, we’d live in a world with no data breaches. What SOC 2 certification proves is that you have processes in place to mitigate potential risks, and that you consider the security ramifications of every decision.
How much does SOC 2 certification cost?
In our case, our original SOC 2 Type I audit cost $27,500, not including the consulting fees. The SOC 2 Type II was slightly more expensive, but required fewer consulting hours, so it more or less evened out. Also, depending on the complexity of the audit, the number can run to over $100,000.
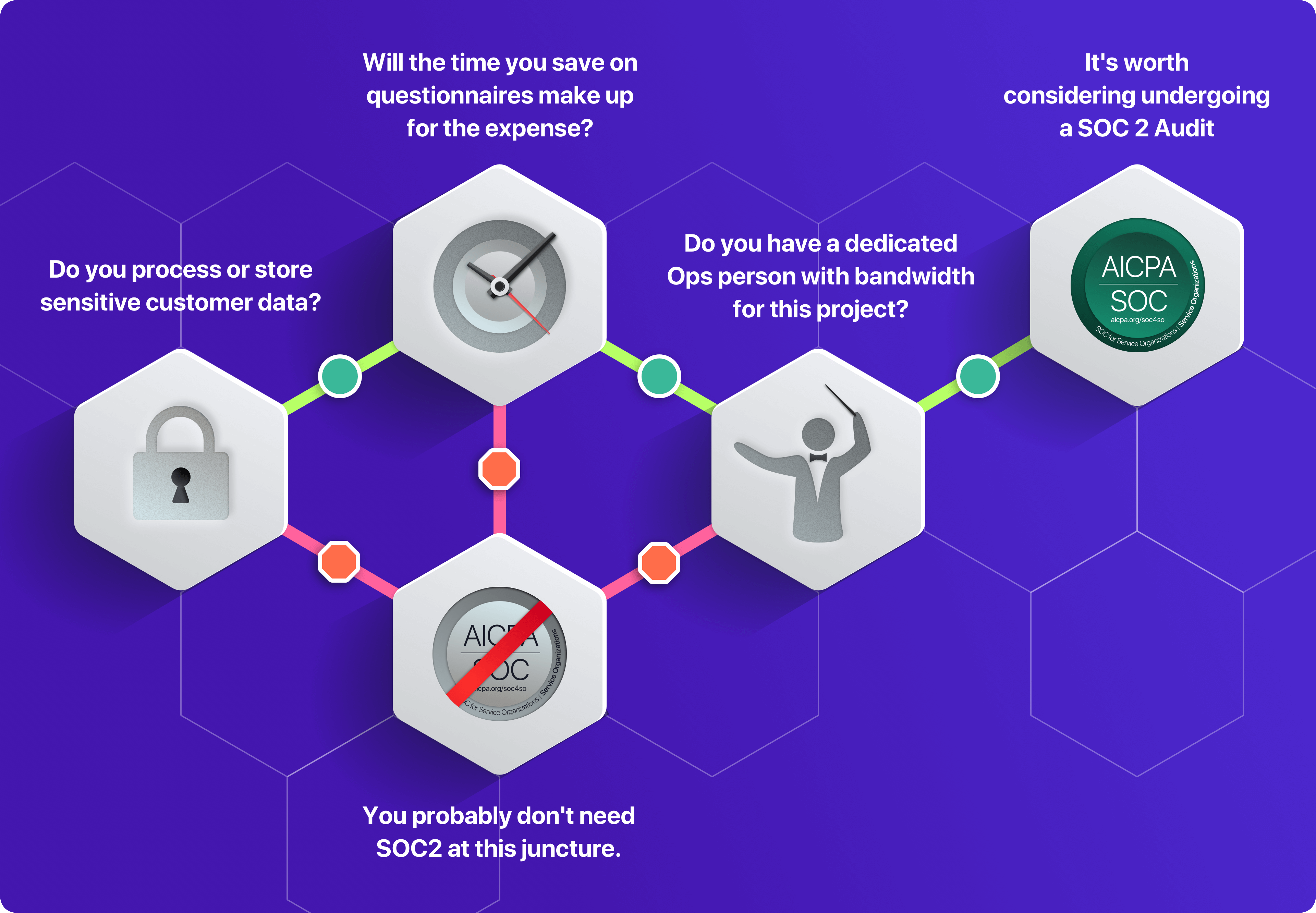
Does my company need SOC 2 certification?
The simplest answer is: it depends. But you definitely shouldn’t get it unless you’re clear on the reasons why, and those reasons should go beyond “everyone else is doing it.”
What was the hardest part of getting SOC 2 compliant?
For me, the SOC 2 process wasn’t difficult as much as it was tedious. Creating new documents, finding overlap between existing ones, and having to ask our auditors endless questions were all time-consuming tasks. Luckily, I’m a relentlessly organized person, so I was up to the challenge. If your startup is so young that you haven’t hired a dedicated ops person yet, you may want to hold off for now.
However, this answer has a major caveat: proving SOC 2 compliance wasn’t particularly challenging for Kolide, because our product is literally designed to do the things SOC 2 is asking for. If you didn’t have Kolide, you might not have an inventory management system, or a seamless alert system when a device contains malware, or evidence of your company encrypting their SSH keys, or enabling their firewall, or having automatic updates enabled. I could go on. Without those capabilities, I imagine compliance would be much more challenging.
If you would like a tool that will make your next SOC 2 audit easier, watch our on-demand demo to see how our Device Trust solution can help.