Two Years at Kolide — Creating a New Privacy Standard for Endpoint Security
On May 22nd, 2019, I posted an article on this blog entitled, “Kolide — User Focused Security for Teams That Slack.” The post was more than just an announcement for our K2 SaaS product; it was a much-needed complete company relaunch after some significant internal turbulence at the start of the year.
Two years later, K2 is the most successful product I’ve personally ever shipped and the product I am the proudest to have worked on in my career. So while I’m generally not one to lay back in my chair and wax on about the past, it felt appropriate to take a minute and reflect on the progress we’ve made and see if there was any insight worthy of sharing.
I began by first re-reading our launch blog post. The first thing that struck me was how few words I would need to change if I were to repost this article today. The problems we set out to solve, the reasons we wanted to solve them, and the primary mechanism of the solution are all identical to the product we sell right now. My description of user-focused security has the surety and clarity of someone who has just finished writing Honest Security; yet I wouldn’t write it for another year and a half.
With that said, another thing struck me. I couldn’t believe how little end-user privacy is mentioned in the post. It’s a topic which would become a major tent-pole of our product strategy. Without our focus on privacy, nothing that we do for our customers would even be possible. How could we have been so right about the vision and yet miss so many of its most important pieces? How were we successful despite these critical omissions?
So instead of writing the typical spiel on “how far we’ve come,” I thought I’d spend time doing something worthwhile and explain “how we got here.”
Held To The Highest Standard
At Kolide, we often have the luxury of pitching prospects already believers in the Honest Security approach. Sometimes though, we encounter folks who have a more cynical view of their fellow employees and question any approach that relies on the end-user’s active participation to accomplish its goals. One reason these people are cynical is that they’ve actually already tried to “do the right thing” for their users and ended up castigated by the very people they’re trying to help. We know this happens because it happened to us when we launched.
As we were building out our Slack-based workflow, we (perhaps somewhat naively) expected to be greeted with enthusiasm by end-users. Our thought was that they would be willing to take some degree of ownership of their devices’ security in exchange for not having it completely locked down by IT. While this assumption was eventually proven correct, we were missing a major piece of the puzzle.
Our first customers forwarded concerns from users who wanted to know how Kolide knew that their device’s firewall wasn’t on. In fact, they wondered what else it might know. Next, more technical users poured through the agent’s source code on Github and looked for any reason to be concerned. Our first reaction was that we felt we were unfairly held to a completely different standard. Our competitors’ closed-sourced agents sit silently on the endpoints and collect as much data as possible. And yet, by being the first to open the curtain a little bit, we suddenly bore the entire weight of solving all of the privacy issues perpetuated by our industry. If this would be a pattern going forward, why not just give up and do the dishonest things our competitors do?
No way.
After thinking through the problem, we realized the most important insight so far in our company’s history: complete honesty and total transparency need to be established before you can expect someone’s help and cooperation. With that realization, suddenly, everything we needed to do to overcome this challenge became clear.
Trailblazing the First Honest Security Features
After our realization, we looked at how poorly suited the traditional endpoint features were for establishing honest relationships with end-users.
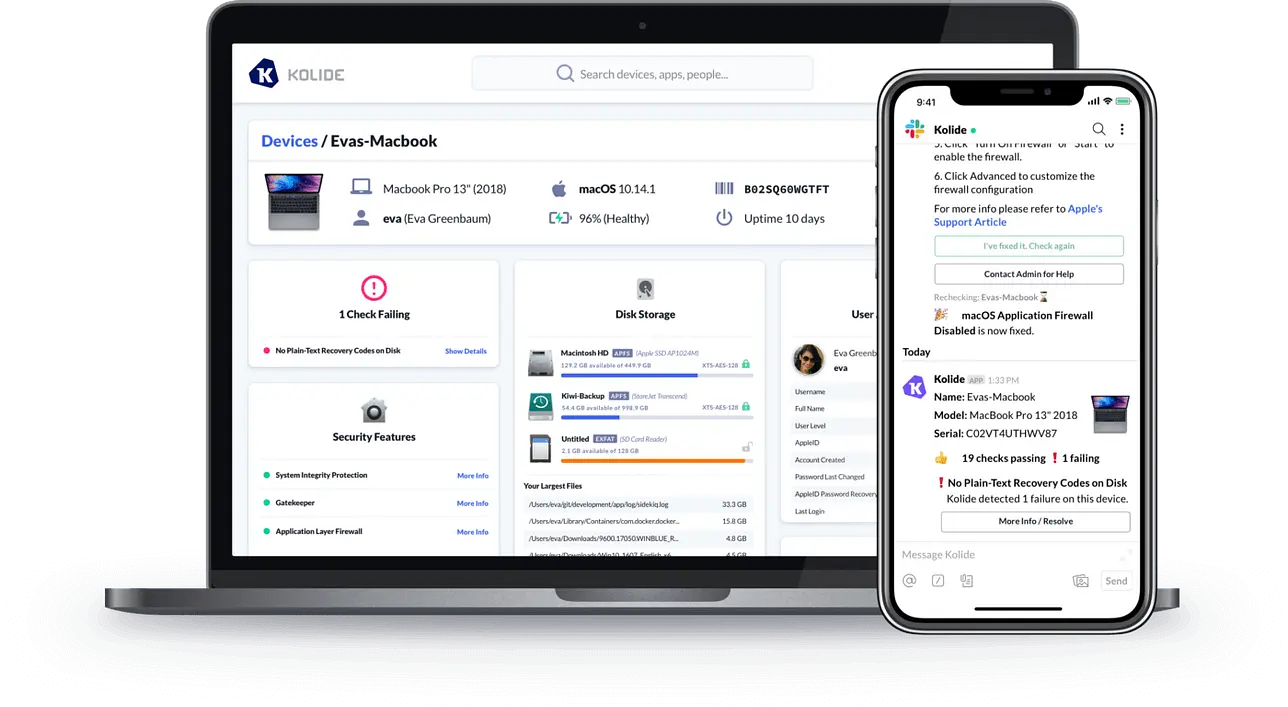
The problems start even before you roll it out. Most endpoint agents are installed remotely by the IT team through management software. As a result, end-users are likely unaware if their device even has an endpoint agent, a major problem when our slack messages would contact them out of the blue with intimate knowledge about the security posture of their device.
We knew that it was important that end-users understood how Kolide received its data from their devices, and what better way to understand that than actually to have them install the agent themselves? That’s exactly what our onboarding flow does.
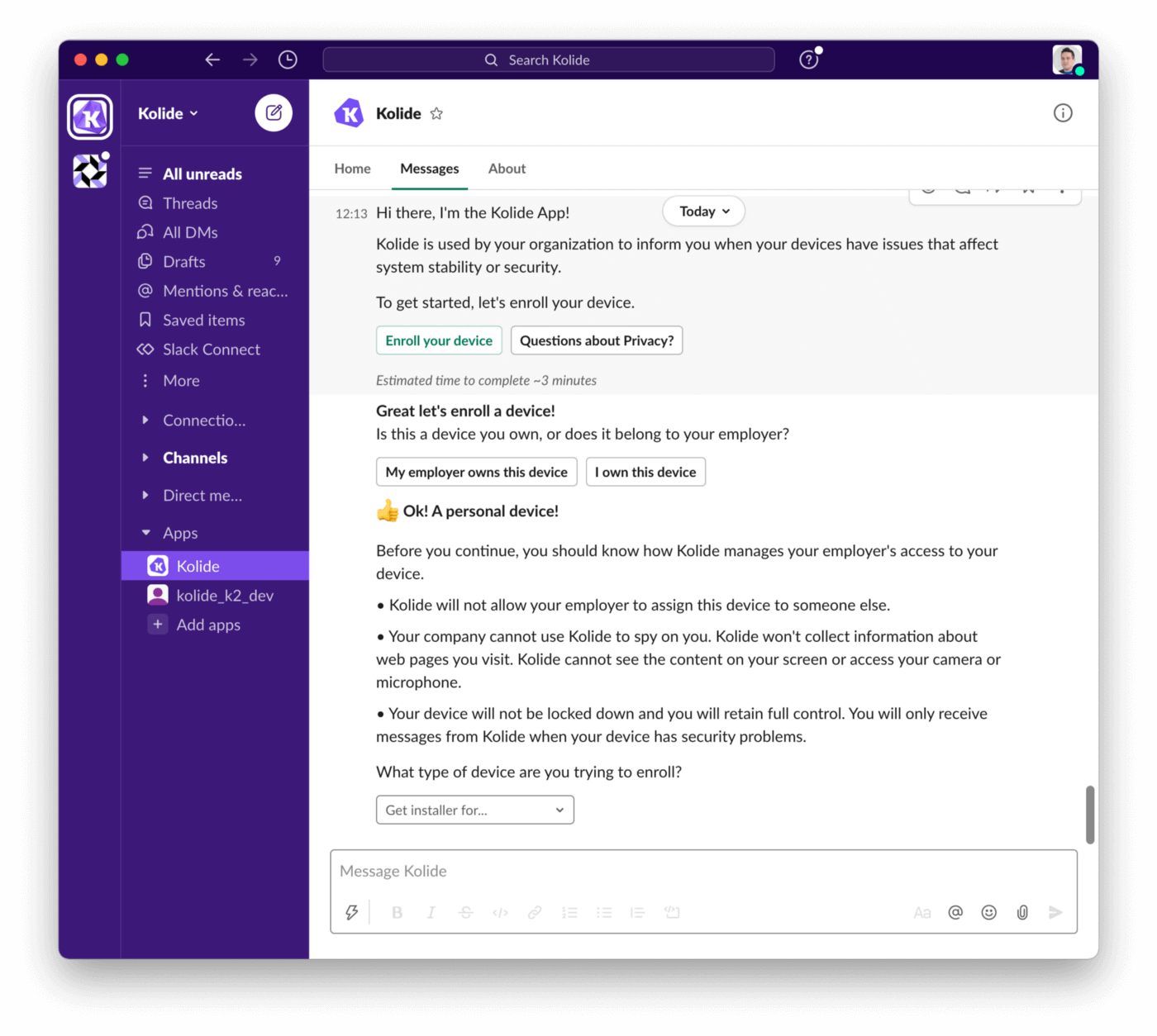
While rolling out this feature enabled end-users to feel in control of the process and understand how data was collected, we still needed to explain what data was collected, and more importantly, why it was collected. These were the main drivers that led to the creation of our end-user privacy center.
In this privacy center, end-users can see exactly what data may potentially be collected from the devices that are currently enrolled. Even more importantly, they can use the privacy center to understand what data will be collected about their device before they enroll it.
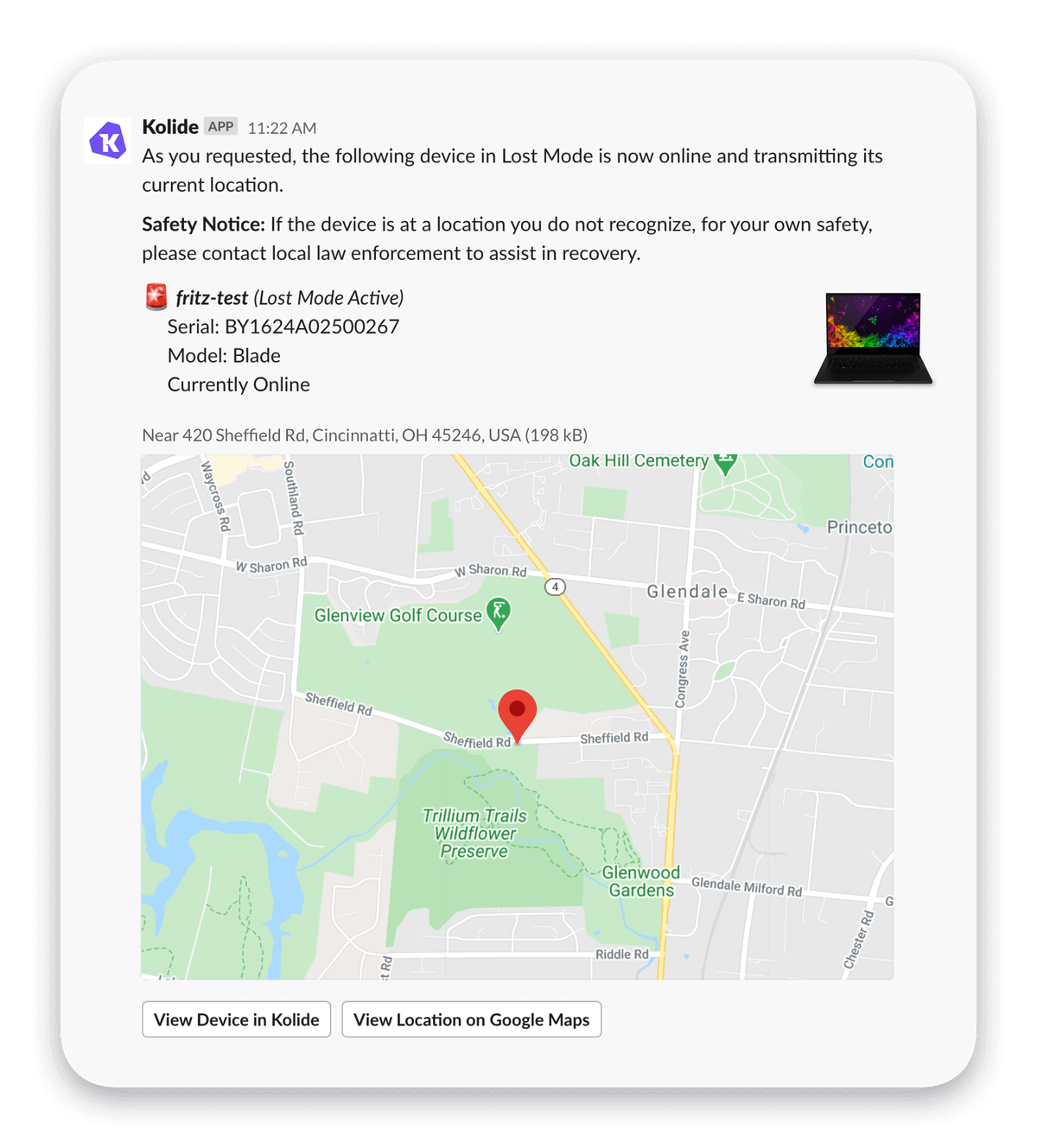
Just like with onboarding, building the privacy center revealed yet another challenge to be solved. We found that sometimes organizations needed to collect very sensitive data when the situation warrants it. For example, if an end-user lost their device, knowing its exact coordinates could lead to its recovery. But just because this was true in one scenario, it didn’t mean that collecting geo-location data continuously could really be justified even in the context of the privacy center.
The solution? We could ask end-users and get their permission for this type of sensitive data collection on an as-needed basis. And that is exactly what our sensitive device actions workflow does.
The Impact of Our Solution
As Kolide grows, we are starting to see an impact on our efforts. After a dozen customers immediately purchased the solution after my blog post two years ago, I knew that we had tapped a raw nerve. What I didn’t know was how quickly sensibilities about end-user autonomy and privacy would shift away from the status quo and embrace the ideals we proselytize. The great migration to working from home has completely recontextualized the often unchecked and invasive capabilities of traditional endpoint management and security products.
This is the power of not just writing about the ideal state but also rolling up your sleeves and writing software that actually helps people get there. That’s always where the real learning happens.
While it still feels like we are just getting started at Kolide, I would be remiss not to acknowledge the progress we’ve made in just a couple of years. To all of our customers, fans, and well-wishers, thank you for your support and feedback.
I can’t wait to share what’s next.