CPRA Will Transform How Your Company Treats Employee Data
If you’re reading this after New Years, the revolution has already happened. You can be forgiven for asking “what revolution?” since this one took place with relatively little fanfare. So let us catch you up.
January 1 marks the debut of the California Consumer Privacy Rights Act (CPRA). The CPRA is a series of amendments to the California Consumer Privacy Act (CCPA), which has been in effect since 2020, and which was hailed as the United States’ first major piece of data privacy legislation. CCPA gave consumers a number of rights and required businesses to develop processes so they could comply with its obligations: to let consumers request copies of their personal information, delete said information, and opt out of its sale (among other things).
Even though CCPA was a landmark law, it’s no secret that plenty of companies didn’t take it particularly seriously, and privacy advocates criticized it as “toothless.” But while CPRA may be known as “CCPA 2.0,” it’s a different animal entirely. And this one has some very sharp teeth.
CPRA is designed for more aggressive enforcement than its predecessors. Changes include:
- Creating a new California Privacy Protection Agency to enforce the law
- Eliminating the 30 day grace period in which companies could correct violations before being subject to enforcement actions
- Adding new rights that bring the law closer in alignment with the EU’s GDPR
But the most significant change to CPRA is that it adds an entirely new protected group: employees.
CPRA does away with CCPA’s so-called “employee exemption,” meaning that if your organization has California-based employees, you’re about to be held to a new standard of transparency.
If you’re not sure the law applies to your company, or if your existing policies will need to change, read on.
CPRA’s Employee Data Rights
Under the new iteration of California’s data privacy law, employers are required to give most of the same data rights to their California-based employees as they do to California customers.
CCPA granted the following rights, which CPRA now extends to employees:
- Right to know: Employees can request copies of the personal information collected about them, and employers must respond within 45 days.
- Right to correct: Employees can correct inaccurate information.
- Right to delete: Employees can request that their personal information isn’t retained, with exceptions for data the employer is legally obligated to retain.
- Right to opt out of sale or sharing: CPRA’s definition of “sale or sharing” is quite broad, so this right includes vendors and service providers who handle employee data, unless they have signed a CPRA agreement with the employer.
CPRA also introduces two new rights:
- Right to limit use and disclosure of sensitive personal information: CPRA introduces the concept of “sensitive” personal data, which is subject to greater protections than mere “personal” data. This category includes things like sexual orientation, race, union membership, biometric data, precise geolocation, and some electronic messages. This right would not prohibit the collection of all such data, but limit its use to reasonable purposes. For example, tracking the number of female employees as part of a DEI initiative would probably be acceptable.
- Right to opt out of automated decision-making technology: This new addition is borrowed from the GDPR, but CPRA leaves it to the new regulatory agency to enumerate the precise opt-out rights employees will have. However, the law does define one type of automated technology,“profiling,” as processing that attempts to analyze or predict “performance at work, economic situation, health, personal preferences, interests, reliability, behavior, location, or movements.” This right could impact the use of automated tools that profile job candidates, particularly if they’re found to biased on the basis of race, sex, or other sensitive factors
- For-profit companies
- Made over $25 global annual revenue last year
- Employ at least one California resident
How to Get Compliant With CPRA
We asked attorney Caroline Morgan of Culhane Meadows, who specializes in advising companies on data privacy and security laws, how companies can prepare for CPRA’s new requirements. She emphasized the importance of a proactive approach, instead of waiting to see how the law is interpreted in court, whether it includes independent contractors, etc.
“Regulators are not looking for perfection but they certainly want to see good faith compliance, which should be thoughtful, planned, and prospective,” Morgan says. “Simply drafting a new privacy policy and hoping that is enough is essentially c rossing your fingers and hoping you are compliant.”
Step 1: Data mapping
The first step in CPRA compliance is to understand what employee data your company collects, where it’s stored, who it’s shared with (both internally and externally), and how long it’s retained.
One serious challenge is that American companies–particularly those who’ve never had to deal with the GPPR–aren’t used to thinking about privacy and data minimization when it comes to their employees. Many companies aren’t even aware that they’re dealing with “sensitive personal data,” because that category doesn’t just include HR records and payroll. The tools you use for security, authentication, and communication can all fall under this umbrella.
The National Law Review writes that “Employment-Related Information may now include things like network monitoring, video surveillance, photographs, and document metadata. It may also [include] biometric data (including fingerprints and face and voice recognition when used to identify or authenticate the employee)…”
Part of mapping all this data includes mapping how it’s accessed and secured, so it’s a good time to make sure you’ve got role-based access control in place, and that no sensitive data is leaking onto personal devices or unapproved applications.
All this to say: don’t underestimate the scope of your data mapping project, and prepare to involve representatives from HR, IT, and operations.
Step 2: Establish processes for handling employee requests
For each type of personal employee data you collect, you need a process in place for when employees request to correct, delete, or see it.
In some cases, this will be straightforward. Some HR data, for example, should exist only within designated tools, and it should be easy to access a copy of an individual record.
In cases where third-party vendors manage employee data, you’ll need to assess whether they have CPRA-compliant processes in place to handle requests you pass on. The National Law Review suggests preemptively amending agreements with vendors such as “benefits providers, payroll providers, building managers, and other similar organizations who may have access to Employment-Related Information.”
Then there are the really thorny situations, where the employee data you collect is difficult to parse, likely to upset employees, or both. Take the example of Slack DMs. As we’ve written, Slack enables employers to download private messages and channels, but these exports tend to come in the form of massive, difficult-to-read files that include all messages from a workspace. You’ll need a process to isolate a single employee’s messages in response to a request, but without compromising the privacy of the other parties they’re messaging.
Moreover, you’ll need to prepare for a backlash among employees who had no idea their DMs were being collected in the first place. Good intentions will only take you so far here. Even if no one ever read those private messages and you conducted the data export for a completely separate purpose, you’re still accountable for all your data collection capabilities.
And that means you might want to assess whether all that data is really necessary.
Step 3: Eliminate unnecessary data collection
The process of data mapping may unearth some practices your workforce is uncomfortable with, or would be if they were aware of them. (And they’re about to be aware of them.)
Obvious examples include so-called “bossware” that surveils employees via webcam or screen monitoring without their knowledge (a disturbingly common phenomenon). But even generally accepted practices, like tools that give IT admins total visibility and control over devices, deserve a second look to ensure they’re minimally invasive.
As you assess these practices, it’s crucial that your approach reflects the reality of remote work. There’s an inevitable bleed between the public and private that’s evident in your browser history, the photos on your work laptop, the personal life in the background of your webcam. It’s practically impossible to prevent personally sensitive information from getting onto company devices, but you can minimize your exposure to it.
Step 4: Be transparent about employee data collection
CPRA doesn’t do much to prohibit specific kinds of data collection or surveillance but it does require more up-front transparency from employers, in the form of a “privacy notice” and a “notice at collection.”
The Mintz law firm’s blog explains the difference: “The ‘notice at collection’ is forward-looking. The ‘privacy notice’ looks back to that information collected by the employer in the 12 months prior to the effective date of the policy and must be comprehensive.”
In both cases, the boilerplate language common to employment contracts won’t be sufficient–be prepared to enumerate what you collect and why.
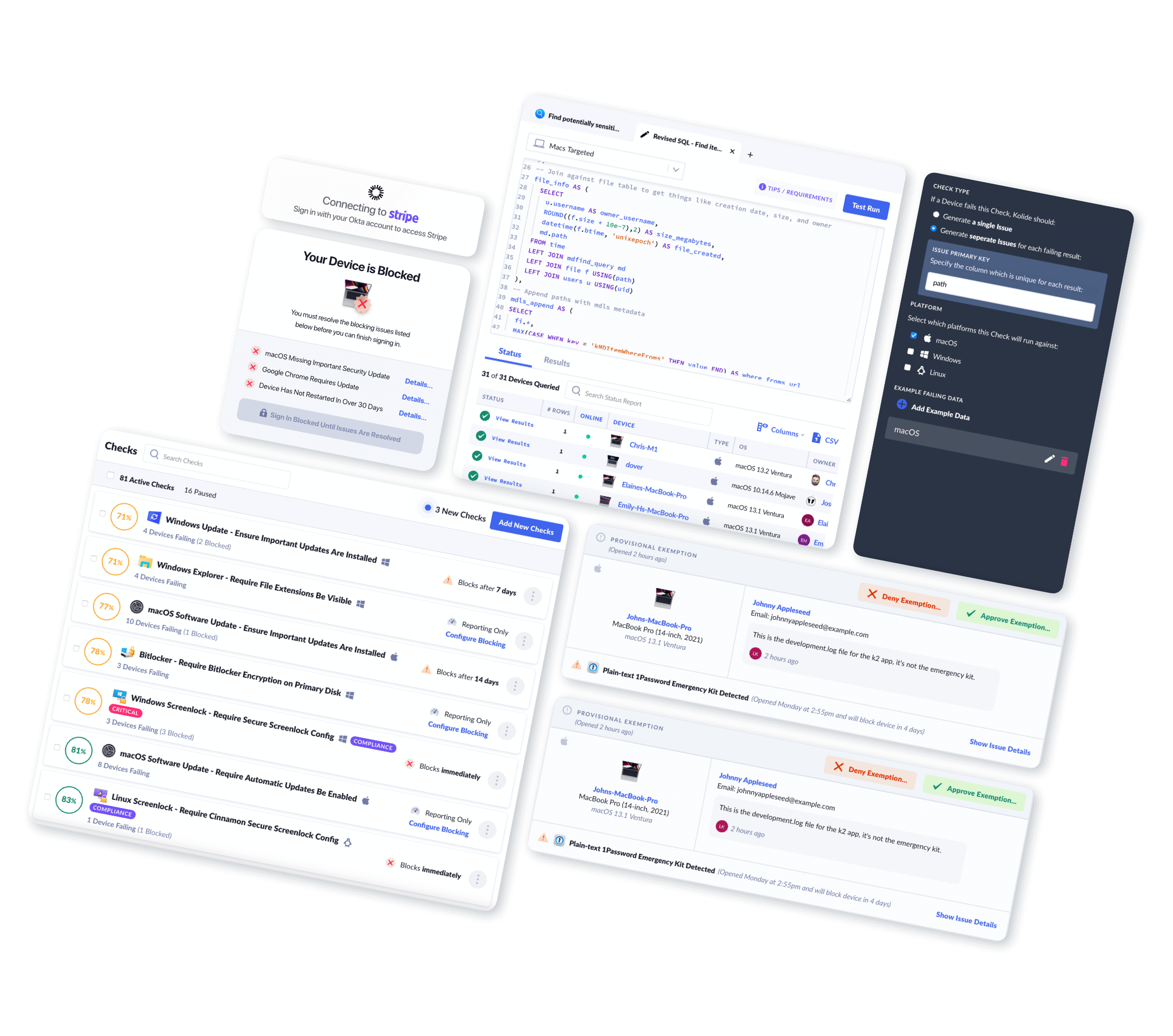
You can give yourself a leg up in this process by working with vendors who are already dedicated to privacy and transparency. Such as, just as a completely random example, Kolide. (Oh come on, we had to mention ourselves at least once.)
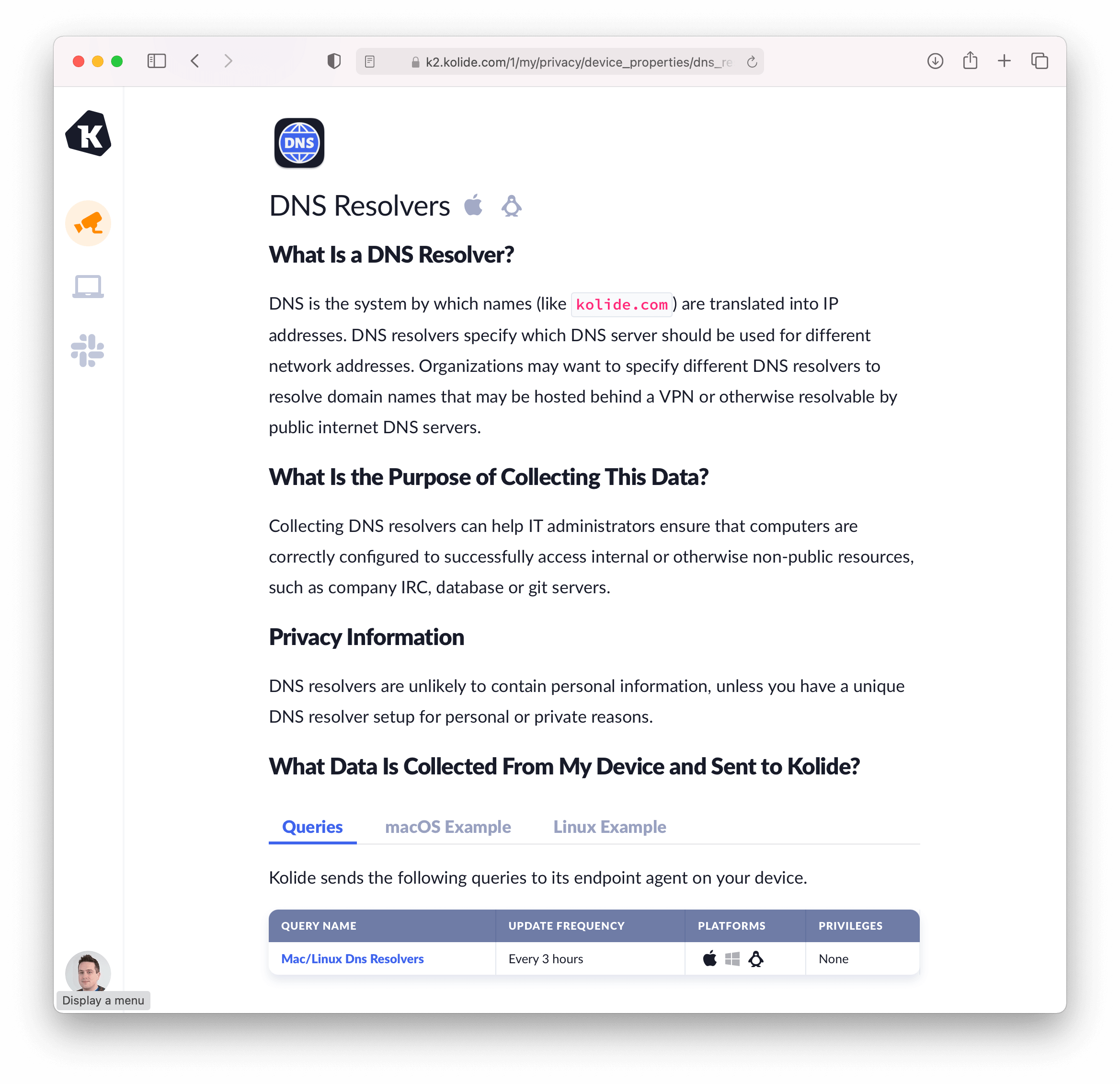
As an endpoint security company, Kolide has to collect data about employee devices in order to enforce compliance. But our product includes a Privacy Center, where employees can see all the data we collected, its purpose, who can access it, and its impact on privacy.
50 states, 50 employee privacy policies?
If your company is based in California, then CPRA is about to be an unavoidable fact of life. But what about remote companies, with just a handful of California employees?
Well, technically you can have a CPRA-compliant set of policies for California, and another for the rest of your workforce. That’s the tactic most companies took for implementing CCPA for consumers, after all. (If you’re a consumer in one of the other 49 states, you’ve probably noticed those “California Residents Click Here” buttons on your favorite websites, and felt vaguely left out.)
But we don’t recommend this fragmented approach, for a number of reasons. For one thing, the CPRA may be a groundbreaking law when it comes to employee data privacy, but it won’t be the last.
“Other states will undoubtedly continue to look at CCPA/CPRA as a model for privacy legislation,” says Morgan. “For example, earlier this year a New York law took effect that requires New York employers engaged in electronic monitoring to give written notice to employees upon hiring regarding surveillance of employee internet usage, calls, texts, and emails and to put information about this surveillance in a ‘conspicuous place.’”
Even if no more employee data privacy laws were in the works, you have to recognize the fact that your employees communicate across state lines. If an employee in California learns about invasive surveillance, the word (and the backlash) will spread. It’s better to get out in front of the narrative.
CPRA Is Leading a Revolution in Employee Data Privacy
There’s a worn-out truism in tech that “Americans don’t care about privacy.” This line gets repeated constantly–quietly by tech CEOs, frustratedly by security professionals, and despairingly by privacy activists. But that phrase doesn’t tell the whole story.
It may be true that American consumers are willing to accept a loss of privacy as the cost of participating in the economy, but that doesn’t mean they don’t care. They only shrug at the constant cycle of data breaches and privacy scandals because they have no way to push back. After all, users can’t exactly march up to Meta headquarters and ask to speak to the manager.
But employees have far greater abilities to band together and assert their rights. And employees care deeply about their privacy. An ExpressVPN survey found that 54% of employees would switch jobs to avoid surveillance.
Plenty of articles describe the expiration of CPRA’s employee exemption as a “burden” on employers, and there’s no denying that getting compliant will take significant effort, including and especially from IT teams. But it’s also a great opportunity to get rid of sensitive data you never really wanted, and to be transparent with your employees about the policies you have.