The Employee's Guide to Slack's Privacy Policy
So here’s the headline: Your boss can read your Slack DMs. Even if you edit them. Even if you delete them. Even if you leave the company.
But even if you’re already dimly aware of that fact, you probably don’t know how the process of accessing your data works in practice.
Unfortunately, you won’t learn much about that from Slack’s privacy policy. That document exceeds 5,000 words, includes 15 subsections, and primarily addresses how Slack itself manages data. (It’s pretty boilerplate stuff.)
For the average employee, the most pressing concern isn’t what Slack is doing with their DMs–it’s what their boss is doing. Employees have questions, such as:
What kinds of data does Slack collect and share with employers?
Who at your organization is allowed to access DMs and private channels?
Does Slack have privacy guardrails to prevent abuse?
Can employers peek inside private conversations on a whim, or do they need to show a valid cause?
The answers to these questions matter because they impact how we behave and what we feel comfortable talking about on Slack. Slack sits at the crossroads of two major trends: a growing labor movement and the rise of remote work, so it’s vital that employees know how to communicate safely and responsibly with coworkers.
Slack’s Approach to Data Privacy
The first thing you need to understand is that Slack’s privacy policies are designed to meet the needs of its customers, which are employers, not employees.
A privacy at Slack landing page, for example, states that “Customer trust is at the forefront of everything we do” and that “You own and control the content within your Slack workspace.” This sounds nice but it’s important to keep in mind that in most cases (outside of community-run Slack instances), the “you” is an employer. Legally, Slack considers itself to be a “processor” of customer data while the customer–your employer–is the data’s “controller.”
This framework is essential both to interpreting Slack’s messaging and understanding how Slack prioritizes the needs of employers versus employees.
Employer Access to Slack Data Varies By Pricing Tier
In theory, Slack allows all workspace owners to request access to private channels and DMs. Slack provides some oversight to prevent abuse, but ultimately, employers are the data’s “controllers.”
However, when you dig into Slack’s help documentation, you find that Slack’s level of oversight is not universal, and varies depending on a workspace’s pricing tier.
In other words: employers have more access to employee data if they pay more for Slack.
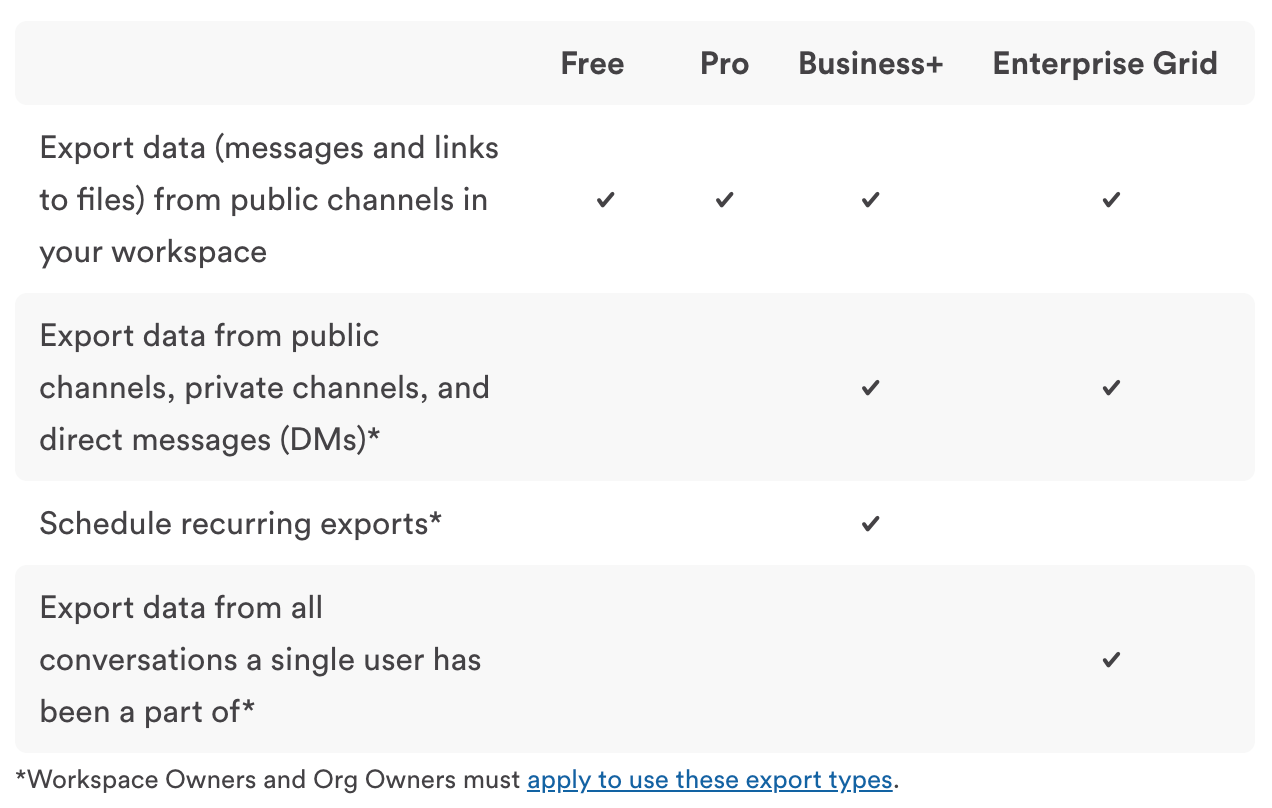
This illustrates how export capabilities vary by plan, but elsewhere, Slack claims that Free and Pro accounts may also request private channels and DMs.
There are some valid reasons for not taking a one-size-fits-all approach to privacy. For instance, certain highly-regulated companies and industries are required to maintain records of all internal communications in case of an audit. However, Slack’s employee-facing information neglects to explain this crucial context to employees. On top of that, there are contradictions in Slack’s own documentation, and we found significant differences between Slack’s published policies and our own experience in requesting a data export.
Note: We requested comment from Slack on this matter, as well as other matters discussed in this piece, but they were unable to respond in time for publication. We will update this piece to include any clarifying information they provide.
https://[YourWorkspaceHere].slack.com/account/workspace-settings#overview.
Free and Pro Plans Limit Data Access
Employers using the Free and Pro plans can access and export data from public channels, including links to files but not the files themselves.
If employers using a Free or Pro plan want access to private channels and direct messages, they must ask Slack directly, and Slack will only provide the data “under limited circumstances.”
Slack claims “we will reject applications” unless Workspace Owners can show they meet one of the following criteria:
- A valid legal process
- The consent of members
- A requirement or right under the law
(As you might have guessed, each of those criteria is open to much interpretation.)
If an employer’s request is approved, they’ll receive a one-time export of data from all channels, delivered as a JSON file. This file will include edited and deleted messages, and messages from users who have been deactivated. It also includes messages to and from members from outside the company, like third-party contractors who are guests in your workspace.
{
"type": "message",
"user": "UTXHL6F8A",
"upload": false,
"ts": "1590101612.000000",
"text": "Hello, this is the message after it was edited.",
"previous": {
"text": "Hello, this is the original message.",
"blocks": [
{
"type": "rich_text",
"block_id": "Bts",
"elements": [
{
"type": "rich_text_section",
"elements": [
{
"type": "text",
"text": "Hello, this is the original message."
}
]
}
]
}
]
},
"original_ts": "1590101603.000300",
"subtype": "message_changed",
"editor_id": "UTXHL6F8A",
"blocks": [{
"type": "rich_text",
"block_id": "O+PJ",
"elements": [
{
"type": "rich_text_section",
"elements": [
{
"type": "text",
"text": "Hello, this is the message after it was edited."
}
]
}
]
}]
}
As you can see, even with Slack’s help, at this level you’re looking at a lot of data delivered in a difficult-to-read format.
Our Experience
When Kolide initially requested a complete data export, we belonged to the Pro
tier, which meant we had to message Slack support through a generic “Contact Us”
form (located at https://[yourworkspace].slack.com/help/requests/new). We were
deliberately vague in explaining our reasons for requesting an export; we said
only we were “investigating a privacy-related matter.”
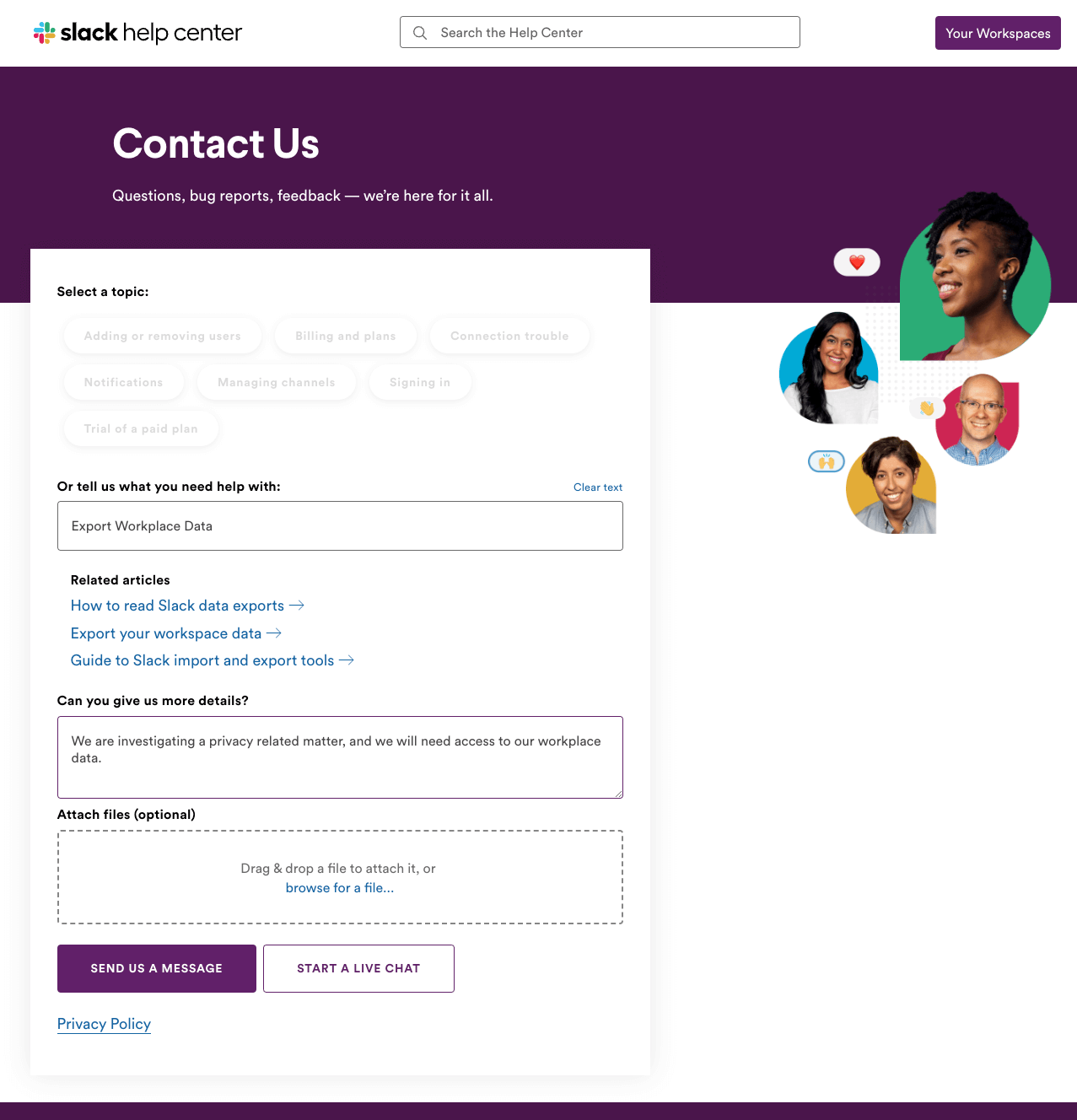
When Slack replied, they did not ask us to prove that we met their requirements for exporting data–they merely said that if we wished to do so, we would have to upgrade to a more expensive plan.
That could have been the end of our investigation. But then we realized we probably needed to upgrade anyway in order to access SAML-based single sign-on. (Whether it’s ethical to charge extra for SSO is another matter.)
Business+ Plans Enable Employers To Export Data At Will
Employers using the Business+ plan also need to apply to Slack to export non-public data. But as opposed to a one-time export, this grants employers access to a “self-serve data export tool.”
It’s worth pausing on the fact that there’s a material difference between having to ask permission every time you want to export DMs, and being able to do so at your leisure. The easier it is to access employee data, the greater the temptation to abuse it.
To use this tool, Slack writes that employers must ensure they have “appropriate employment agreements and corporate policies” and only use the tool as permitted by applicable law.
The most important word here is “ensure.” Whereas at the Free/Pro levels, Slack writes employers must “show” they meet certain requirements, here, they need only to say they will use this tool responsibly.
Our Experience
Once we upgraded to the Business+ plan, Slack support said the next step was to submit an application for the data export tool, which would be reviewed by a “dedicated team.” They wrote: “There are several factors considered in the review process, and applications are handled on a case by case basis.” That language seemed to imply we could expect a drawn-out review process, but that’s not what we found.
Slack’s “application” for the data export tool turned out to be a three-page legal document that essentially establishes two things:
The employer attests that they have the authority to access this data in accordance with the law, and that they have “obtained the appropriate permissions, as set forth through employee handbooks, computer use policies, consent forms or similar documents or electronic notices, to obtain access to all of its employees’ communications carried or maintained on Customer’s networks and systems…”
The employer agrees that Slack will not be responsible for any damages related to this agreement, including liabilities arising from employees or regulators. “For clarity, this includes any claims arising out of any failure by Customer to secure the appropriate permissions from its employees, whether in the United States or elsewhere, to export employee communications.”
We duly signed this document. Next, Slack requested an email from our Workspace Primary Owner (in this case the CEO), acknowledging that this export will contain all message history, and that all Workspace Owners will have access to the export tool.
https://[yourworkspace].slack.com/account/workspace-settings#admins
We weren’t sure what to expect next, but less than four hours later, Slack informed us that our application had been approved and we could export data as we saw fit. We thanked them for their help and then promptly asked them to disable the tool, since reading private messages is not a capability we have any desire to maintain.
Enterprise Grid Plans Enable Easier, Deeper Data Collection
Our personal experience with Slack’s data export process ended at the Business+ tier, but their help documentation outlines what customers at the Enterprise Grid level can expect.
Employers using the Enterprise Grid plan must also apply for access to the self-serve data export tool if they want to see private messages and channels. However, these VIP customers get to send their applications straight to the support team instead of submitting an application through the Slack app.
There are a few significant upgrades at this level, including:
- Employers can export data for a single user, instead of all users
- Data can be exported via either JSON or TXT format
- Whereas every other export only includes file links, TXT includes the files themselves
The Discovery API
But the biggest difference between the Business+ plan and the Enterprise Grid plan is that employers paying for the latter get access to the Discovery API.
The primary goal of the Discovery API is to enable employers to connect Slack to approved, third-party eDiscovery and data loss prevention tools (and the primary goal of those tools is to help companies meet data management regulations).
The former, eDiscovery, captures and stores messages and files from Slack in a third-party data warehouse. The latter, data loss prevention, scans messages and files for policy-breaking content, so companies can catch people sharing sensitive data like credit card and social security numbers.
For example, Hanzo, a company that provides risk management software, has a product called Hanzo Hold that helps employers “securely collect relevant Slack data and metadata, including embedded content, threaded conversations, edits, deletes, and other changes over time.”
Compliance Admins and Legal Holds
The Enterprise Grid plan offers more administrative roles than other plans–one of them being the “Compliance Admin system role.” This person, who’s given their powers by the organization’s primary owner, can create and manage legal holds.
A compliance admin can place a legal hold on any employee and a legal hold preserves an employee’s messages and files. When a hold is active, compliance admins can either retain message and file data from all conversations or just the direct messages from the conversation the targeted employee is a part of. No matter what general retention settings might be in place or whether an employee edits or deletes content, a legal hold ensures all messages and files sent by all members in a given conversation are saved. Once compliance admins retain this data, employers can export it or access it via the Discovery API.
Slack explains too, in a magic wand adorned tip, that there is “no limit on the number of legal holds you can create.”
We should note too, that on this page, Slack doesn’t explain or define the “legal” aspect of a legal hold.
Our Thoughts on Slack’s Approach to Employee Data Privacy
Before we go any further, let’s try and find some nuance in how Slack shares data with your boss, because it’s not a black-and-white issue.
Take our own experience getting access to Slack’s export tool. Slack did not provide the level of oversight we expected. We did not have to prove we were behaving ethically; we merely had to say we were. But that’s not really surprising once you think about it, since Slack has no way of investigating every request it receives. How could they possibly tell if an employer is really investigating harassment or merely using it as a pretext to sniff out union activity? At a certain point, every company has to trust its customers not to abuse its products; if not, society would grind to a standstill.
But even if we assume that the vast majority of employers are behaving ethically, and that Slack’s policies are fundamentally sound, we can still take issue with their lack of transparency toward end users.
Slack’s privacy policy is evasive when it comes to employee privacy, and its help documentation isn’t intended for or easily discoverable by employees. This creates confusion, and that confusion opens employees up to risk.
Fundamentally, employees can’t make informed decisions about how to behave on Slack without understanding who is looking over their shoulder. Slack doesn’t precisely hide the fact that it gives employers surveillance powers, but there’s a pervasive sense that it’s an uncomfortable topic that Slack would prefer users didn’t think about too hard.
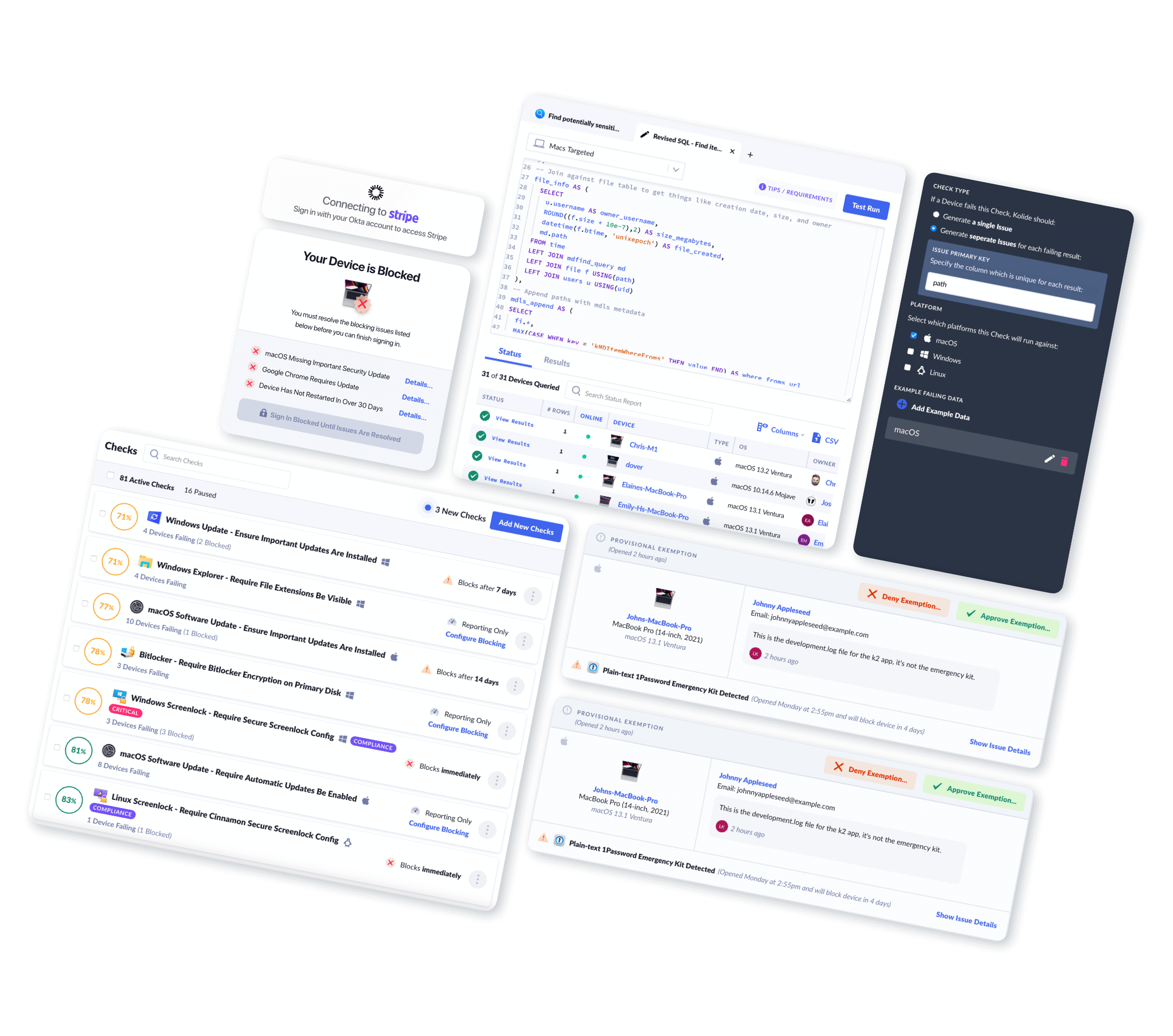
Our product, Kolide, also collects employee data in the name of endpoint security; we can see when you last rebooted your computer, whether you’ve installed updates, and even search for specific files. The difference between us and Slack is that transparency and informed consent–what we call Honest Security–are at the heart of everything we do.
It also bears mentioning that we use Slack at Kolide, both internally and as a part of our product. Slack is ubiquitous, and it’s far from the only tech company who fall short on matters of employee data privacy. So it’s not feasible to suggest that anyone with a criticism of Slack (or Facebook or Google or Apple) just goes elsewhere–it’s incumbent on us to encourage them to do better.
How Third Parties Access Slack Data
Most of Slack’s third-party sharing is pretty benign–or at least it’s as benign as a typical tech company. For example, Slack shares data with some subprocessors that keep the platform functioning, like AWS.
Slack also shares data to serve its “legitimate interests” (i.e. interests that Slack deems “not outweighed by your interests or fundamental rights and freedoms”). Within this legitimate interests section, Slack notes multiple times whether a given legitimate interest is in your interest, Slack’s interest, or is in both of your interests.
For example, Slack argues that “It is in our interest to research and improve the Services” but also that “It is in the interests of Customers and Authorized Users to practice data minimisation and privacy by design in respect of their information.” The responsibility to minimize Slack’s access to your data, in other words, is up to you.
Legal obligations
Slack reserves the right to share data if they are legally required to do so, but it appears to treat requests from law enforcement quite differently than private citizens.
So what if you, as an employee (or ex-employee), want to access data?
If you’re an individual requesting data, Slack rather curtly writes: “Third parties seeking Customer Data should contact the Customer regarding such requests. The Customer controls the Customer Data and generally gets to decide what to do with all Customer Data.” An exception to this rule would be if you have a legal right to access this data under GDPR.
Slack’s policy page goes into much greater depth about how the company handles requests from law enforcement. They explain that Slack requires a search warrant issued by a legitimate court before it will provide anyone with customer data. Slack is clear: “Slack does not voluntarily disclose any data to governmental entities unless” (there’s always an ‘unless’) “there is an emergency that involves imminent danger or there is potential harm to Slack’s services or customers that providing customer data can potentially help prevent.”
Slack notes that it uses all the information it collects to comply with legal obligations. In other words, that data would go beyond the exports employers can access, and include things like metadata and geolocation.
Even then, Slack does not honor every request. The company provides a transparency report that shows what requests it has received and how it responded to them. In the United States, from January 1 to December 31, 2021, Slack has received five search warrants, four court orders, and twenty two government subpoenas. Slack has provided customer data in accordance with those requests in five cases (out of 31 total). This relatively low rate of cooperation would seem to indicate that Slack is willing to fight to protect the privacy of employers, at least.
How Slack’s Privacy Policies Have Evolved
Some of the best advice we can give you about Slack’s data privacy policies is to monitor them for changes.
Slack maintains a privacy policy archive that stretches back to 2013. Though we won’t detail the precise evolution of Slack’s privacy policy over time, it’s worth showing the level to which Slack is willing to change things.
In a privacy policy update released in 2018, Slack made a major change to message access that broke headlines. From 2014 to 2018, Slack customers (or at least, those who bought a premium plan) were able to download and read messages sent through Slack by downloading a so-called “compliance export.” When customers requested a compliance export, employees were automatically notified.
But in 2018, Slack discontinued the compliance export function and introduced the self-service export tool, allowing employers to export data whenever they chose.
At the same time, Slack stopped automatically notifying employees of these exports, leaving it up to employers to police themselves. This raised some eyebrows, but Slack claimed they made the change to comply with GDPR and to help employers conduct private investigations into sensitive matters.
Still, there’s reason to hope that future changes to Slack’s policies may increase transparency. California’s data privacy law (CPRA) is likely to increase Slack’s obligations to employees. So keep an eye on this subject in the coming months and years.
How Should You Conduct Yourself on Slack?
We’ve thrown a lot of information at you (and this is the readable, summarized version), so we’d be remiss to not provide some guidance for how employees should actually use Slack and stay safe at the same time.
Foundational to suggesting or applying any advice is knowing that, despite the privacy policy, Slack is contested legal territory for both employees and employers. Furthermore, your vulnerability and privacy are as much dependent on your employer as on Slack.
Employees at Activision Blizzard, for example, have filed multiple unfair labor practice (ULP) complaints because of manager conduct on Slack, accusing the company of illegally forbidding and punishing discussion of labor conditions and organizing efforts.
Apple, controversially, barred a pay transparency channel on Slack, putting them in a legally murky position.
Slack is also subject to regulations like the General Data Protection Agreement (GDPR) and the California Consumer Privacy Act (CCPA), which means that depending on where you reside, you might have different rights you can exercise, including the right to see what information your boss has requested about you.
Given the evolving legal issues at play, we can’t provide universal advice to employees. What we can do, however, is provide a guiding question to help you make your own decisions: Which conversations should be on Slack and which should be off Slack?
Workplace organizing
Labor organizing is surging in the United States, among tech companies in particular. Potential organizers are likely considering Slack as a way to communicate to fellow workers, especially on remote teams where there isn’t a physical water cooler to huddle around.
We want to make clear that discussing your working conditions at work is a federally protected right. As one labor lawyer said regarding Apple’s case: “If two or more employees are talking about workplace conditions, then they’re protected by the NLRA.”
That said, because your employer can potentially access all of your conversations on Slack without your consent and without notifying you, it’s smart to take conversations about organizing offline. Remote workers may not have this option, but can still move to different platforms, such as Signal, Discord, or even a separate, worker-run Slack instance. If possible, you should also conduct these activities off of your work-managed laptop or mobile device.
Conversations involving company information
Part of what makes Slack both appealing and dangerous is that it feels so casual; you can share files and information without pausing to consider security. But once you’ve shared something, it can disappear into another user’s downloads folder, or any number of unsecure places.
So remember: any time you’re handling sensitive company data (things like valuable IP or customer data), be careful where you’re doing it. If you’re taking data off company-managed applications, you not only open the company up to security risks but potentially make yourself liable.
You should be especially wary if you’re in the healthcare or finance fields, both of which have their own strict regulations. Eleven bankers and brokerages admitted, for example, in September 2022, to using banned messaging apps and had to pay a total of $1.8 billion in fines.
Conversations about other employees
Collaboration within a company inherently requires talking to and about other employees–not always in front of them–but there’s a spectrum between acceptable and unacceptable versions of this conversation.
Gossip, especially if it’s about something you’d be uncomfortable with your boss seeing, likely shouldn’t be on Slack. If you you have serious concerns about a coworker, such as sexual harassment or other inappropriate behavior, your HR department is likely a better place to have this conversation than Slack DMs.
And if the concern rises to a level where you’re not comfortable talking to your manager or your HR department, then you might need to step back and assess how big the problem is. Depending on the severity of the problem, it’s likely best to take this conversation off Slack and hire a lawyer or other outside professional.
Nonwork conversations
Many companies have #random channels and other venues to encourage
non-work-related conversations. Participate in these at your discretion, as
long as you know that your conversations always have the potential to be
accessed.
And even if your messages aren’t objectionable, the amount of non-work messages might be. Employers might not care about the content of your nonwork conversations but care deeply about how much time you’re messaging your friend about your weekend plans instead of working. While Slack isn’t primarily intended as a productivity monitoring tool, it can be used that way.
Slack is One Battleground in a Larger Conflict
The issue of data privacy in the workplace isn’t exclusive to Slack; Slack didn’t even exist the first time someone quipped that you shouldn’t send anything in an email you wouldn’t want appearing in the New York Times.
Traditionally, US laws and workplace culture have heavily favored employer rights over employee privacy, with the assumption that employees only have a “reasonable expectation of privacy.” What the case of Slack makes clear is that we desperately need to redefine what “reasonable” means in the context of remote work.
Think of it this way: in a traditional office, it’s reasonable to expect that your boss can monitor your emails. But you don’t expect them to install recording devices in the bathroom, or follow you to the bar down the street and write down everything you say during happy hour.
But in a remote workplace, there isn’t a bar where you can blow off some steam; you don’t have a reasonable expectation of privacy in any of your communications with coworkers. You are deprived of the universal need to connect on a personal level, to laugh at your manager, to vent.
The result of such a stifling, paranoid environment is either that workers feel disconnected from one another or that they sneak off to alternative digital venues to escape surveillance. Either outcome is an organizational failure.
And while it would be nice to simply trust that employees have nothing to fear from their employers, there’s a clear appetite for surveillance fuelling the growth of the “bossware” sector. ExpressVPN research shows that 78% of bosses/executives use “employee monitoring software to track employee performance and/or online activity” and 73% say “stored recordings of staff’s calls, emails, or messages have informed an employee’s performance reviews.” Even if you’re reading this and thinking “my boss wouldn’t do that,” there’s no telling what your next boss might try, as Twitter employees learned the hard way.
It can be alarming to discover how limited your privacy rights are as an employee. If you’d like to change that, the best way to start is by talking to your coworkers about your concerns. And if you do so, consider taking the conversation off Slack.
FAQ
Let’s review some of the most common questions employees have about privacy on Slack.
Can Slack read my direct messages and private channel messages?
Yes. Slack doesn’t give employers this visibility out of the box but employers can request access. This process varies based on a workspace’s pricing tier.
How long does Slack retain data?
Slack gives workspace owners broad control over data retention. For paid plans, owners can choose for Slack to keep everything, keep everything except edits and deletions, or delete messages after a set amount of time. (Some organizations, like banks, are required to retain all records and export them in a readable format, which basically obligates them to purchase a higher tier of Slack.)
Does my employer need my consent to access my direct messages and private channel messages?
Legally speaking, they probably already have your “consent.” Most employment agreements, especially in the US, include blanket language that gives employers access to your behavior while using company systems and devices.
Will Slack inform me if my employer has exported my DMs and private channels?
No. In the past, Slack informed employees, but changed this policy in 2018.
Does Slack provide user data to advertisers?
Yes. On Slack’s cookie table page, advertising partners include Facebook, LinkedIn, and Google.
Is Slack subject to GDPR or CCPA?
Yes. Refer to Slack’s GDPR page and CCPA page for more information.
Has Slack revealed customer and user data to government agencies?
Yes. In its transparency report, Slack reveals that in the United States, from January 1 to December 31, 2021, it has received five search warrants, four court orders, and twenty two government subpoenas. Slack has provided customer data in accordance with those requests in five cases (out of 31 total).
If you’d like to read more data privacy and security stories like this, sign up for our biweekly newsletter.