How to List TPM Chips Across All Windows Devices
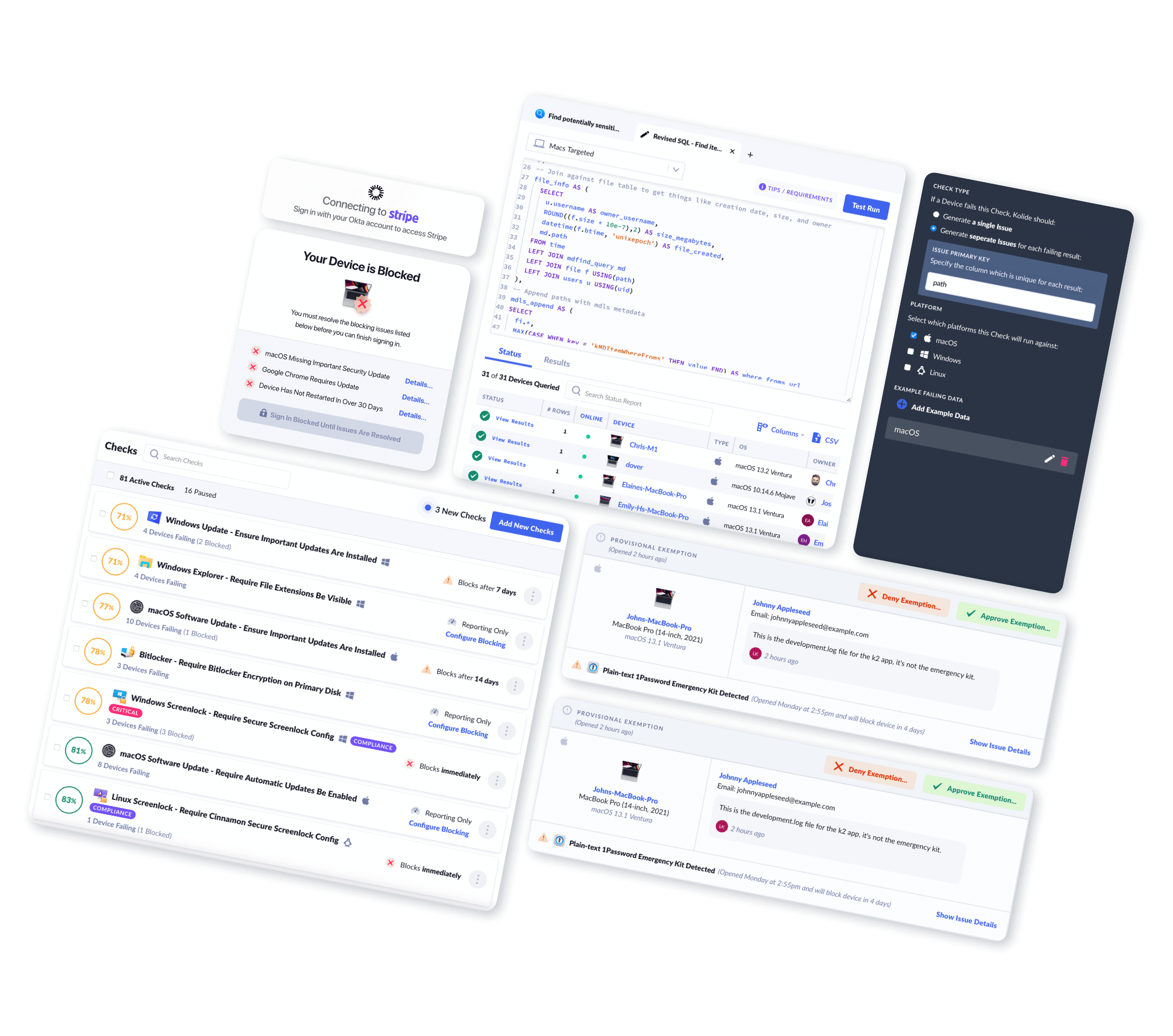
Using Kolide, you can easily view and query TPM Chips across your fleet.
Introduction
A TPM (Trusted Platform Module) is a computer chip that can securely store artifacts used to authenticate a Windows machine by using hardware-based cryptography.
Examples of such artifacts include passwords, certificates, and encryption keys. Once the TPM in enabled, it helps to provide full-disk encryption capabilities.
What TPM Chip Data Can Kolide Collect?
Kolide's endpoint agent bundles in osquery to efficiently collect TPM Chips from Windows devices in your fleet. Once collected, Kolide will parse, clean up, and centrally store this data in Inventory for your team to view, query, or export via API.
Kolide meticulously documents every piece of data returned so you can understand the results.
TPM Chips Schema
| Column | Type | Description | |
|---|---|---|---|
| id | Primary Key |
Unique identifier for the object |
|
| device_id | Foreign Key |
Device associated with the entry |
|
| device_name | Text |
Display name of the device associated with the entry |
|
| activated | Boolean |
|
|
| enabled | Boolean |
|
|
| manufacturer_id | Integer |
The identifying information that uniquely names the TPM manufacturer in integer format. Note: This integer value can be translated to a string value by
interpreting each byte as an ASCII character. For example, an integer value
of Special Values:
|
|
| manufacturer_name | Text |
The identifying information that uniquely names the TPM manufacturer in text format |
|
| manufacturer_version | Text |
The version of the TPM, as specified by the manufacturer Special Values:
|
|
| owned | Boolean |
|
|
| physical_presence_version | Text |
The version of the Physical Presence Interface, a communication mechanism used to run device operations that require physical presence, that the computer supports. Special Values:
|
|
| physical_presence_version_major | Bigint |
|
|
| physical_presence_version_minor | Bigint |
|
|
| product_name | Text |
Product name of the TPM |
|
| spec_errata | Float |
The errata portion of the Trusted Computing Group (TCG) specification that the TPM supports. |
|
| spec_info | Text |
The Trusted Computing Group (TCG) specification that the TPM supports. This value includes the major and minor TCG specification version, the specification
revision level, and the errata revision level. All values are in hexadecimal. For example, a
version information of Special Values:
|
|
| spec_revision | Float |
The revision portion of the Trusted Computing Group (TCG) specification that the TPM supports. |
|
| spec_version | Float |
The version portion of the Trusted Computing Group (TCG) specification that the TPM supports. |
|
| collected_at | Timestamp |
Time the row of data was first collected in the database |
|
| updated_at | Timestamp |
Time the row of data was last changed in the database |
|
What Can You Do With This Information?
Kolide enables you to write your own queries against the data the agent collects. This allows you to build your own reports and API endpoints. For example, you can:
SELECT
devices.name AS device_name,
devices.id AS device_id,
devices.hardware AS device_hardware
FROM
devices
LEFT JOIN device_tpms ON devices.id = device_tpms.device_id
WHERE
devices.type = 'WindowsDevice'
AND device_tpms.id IS NULL
-- Only include devices that have checked in to Kolide since we've been collecting TPM data
AND devices.last_seen_at > '2022-07-01';| device_id | device_name | device_hardware |
|---|---|---|
| 1 | Dobby's Computer | XPS 13 9310 |
| 2 | KOLIDE-X1-CARBON-G3 | ThinkPad X1 Extreme Gen 3 |
-- Microsoft recommends TPM 2.0 or above
-- For more information see: https://docs.microsoft.com/en-us/windows/security/information-protection/tpm/tpm-recommendations
SELECT
spec_info,
devices.name,
devices.id,
devices.hardware,
device_tpms.spec_info
FROM device_tpms
JOIN devices ON device_tpms.device_id = devices.id
WHERE device_tpms.spec_version < 2.0;| id | name | hardware | spec_info |
|---|---|---|---|
| 1 | Adam's PC | Surface Book | 1.2, 2, 3 |
| 2 | DESKTOP-ABC123 | ThinkPad X1 Yoga (1st Gen) | 1.2, 2, 3 |
SELECT
device_name,
device_id,
enabled AS tpm_enabled,
activated AS tpm_activated,
owned AS tpm_owned
FROM
device_tpms
WHERE
enabled = false
OR activated = false
OR owned = false;| device_id | device_name | tpm_owned | tpm_enabled | tpm_activated |
|---|---|---|---|---|
| 1 | Wolfgangs-HP | false | false | false |
| 2 | Quinn-Test-PC | false | true | true |
| 3 | lenovo-thinkpad | false | true | true |
Why Should I Collect TPM Chips?
IT & Security administrators may review information about the TPM for several reasons:
- Verifying that the TPM is enabled.
- Verifying that the TPM is activated.
- Verifying TPM ownership.
- Verifying TPM product and manufacturer information.
- Verifying the PC meets the minimum requirements for Windows 11 and above.
For more information, please read https://www.kolide.com/blog/windows-11-security-and-tpm-2-0-what-you-need-to-know.
End-User Privacy Consideration
Kolide practices Honest Security. We believe that data should be collected from end-user devices transparently and with privacy in mind.
When you use Kolide to list TPM Chip data from end-user devices, Kolide gives the people using those devices insight into exactly what data is collected, the privacy implications, and who on the IT team can see the data. This all happens in our end-user privacy center which can be accessed directly by employees.